Cybersecurity Board Reporting: Executive Dashboard & Metrics Guide 2025
Quick Answer
Cybersecurity board reporting transforms complex technical security metrics into business-focused insights that enable directors to make informed governance decisions. With new SEC requirements mandating cybersecurity disclosure and oversight, boards need standardized reporting frameworks that communicate risk in financial terms, demonstrate program effectiveness, and ensure regulatory compliance. Effective cybersecurity board reporting includes risk quantification, incident summaries, compliance status, budget performance, and strategic recommendations presented through executive dashboards that bridge the communication gap between technical security teams and business leadership.
The Board’s Cybersecurity Oversight Challenge
Cybersecurity board reporting has evolved from an optional IT update to a critical component of corporate governance and regulatory compliance. The transformation reflects the escalating business impact of cyber threats and growing recognition that cybersecurity represents a fundamental enterprise risk requiring board-level oversight.
The Governance Imperative
Modern cybersecurity threats pose existential risks to business operations, financial performance, and stakeholder trust. The global cybersecurity market is projected to grow from $218.98 billion in 2025 to $562.77 billion by 2032, reflecting the urgent business need for comprehensive risk management at the highest organizational levels.
Board directors increasingly recognize cybersecurity as a strategic enterprise risk rather than a technical operational concern. Research indicates that 70% of board directors now view cybersecurity as “a strategic, enterprise risk,” while 44% of executives consider cybersecurity strategy a board-level issue. This shift demands sophisticated reporting mechanisms that translate technical security metrics into business intelligence that informs governance decisions.
The Communication Gap
Despite growing awareness of cybersecurity’s strategic importance, significant communication gaps persist between technical security teams and board directors. When surveyed about their confidence in assessing cyber risk, board directors averaged just 6.5 out of 10, indicating substantial room for improvement in how cybersecurity information is presented and understood at the governance level.
The challenge stems from fundamental differences in expertise and perspective. Security professionals naturally focus on technical metrics like vulnerability counts, patch compliance rates, and security tool effectiveness. Board directors require business-focused insights including financial impact assessments, strategic risk evaluations, and operational performance indicators that align with their governance responsibilities.
Market Forces Driving Change
Several converging factors have elevated cybersecurity board reporting from best practice to business necessity:
Escalating Threat Landscape: Cybercrime costs reached $8 trillion in 2023, with annual costs projected to rise to $10.5 trillion by 2025. Nearly one in three Americans reported falling victim to online financial fraud in 2023, with the highest incidence among individuals aged 35-54 at 36%.
Regulatory Requirements: New SEC rules require public companies to disclose cybersecurity governance structures, risk management processes, and material incidents within specific timeframes.
Financial Impact: The average ransom payment increased 500% from $400,000 in 2023 to $2 million in 2024, demonstrating the escalating financial stakes of cybersecurity incidents.
Investor Expectations: Institutional investors increasingly evaluate cybersecurity governance as part of their investment criteria, viewing effective cyber risk management as an indicator of overall management competence.
SEC Requirements for Cybersecurity Board Reporting
The Securities and Exchange Commission’s cybersecurity disclosure rules, effective since late 2023, establish comprehensive requirements for public companies regarding cybersecurity governance and incident reporting. Understanding these mandates is essential for developing compliant and effective board reporting frameworks.
Material Incident Disclosure Requirements
Public companies must now disclose material cybersecurity incidents on Form 8-K within four business days of determining materiality. This timeline creates significant pressure on organizations to rapidly assess incident impact, coordinate response activities, and prepare accurate public disclosures while managing the immediate operational crisis.
The materiality determination process requires sophisticated evaluation frameworks that consider multiple impact dimensions. Organizations must assess financial consequences, operational disruption, data compromise scope, regulatory implications, and reputational damage potential. Board involvement in materiality determinations ensures governance-level oversight of disclosure decisions and alignment with broader risk management strategies.
Annual Cybersecurity Governance Disclosures
Beyond incident reporting, SEC rules require annual disclosure of cybersecurity risk management strategies, governance structures, and board oversight processes. Companies must describe their approach to identifying, assessing, and managing cybersecurity risks, including the integration of cybersecurity considerations into business strategy and operations.
Board oversight disclosures must detail the governance structure responsible for cybersecurity risk management, including board committee assignments, director expertise qualifications, and oversight processes. Organizations must explain how boards receive cybersecurity information, the frequency of security discussions, and the integration of cybersecurity considerations into strategic planning and risk management decisions.
Board Expertise and Qualifications
SEC rules require disclosure of whether board members possess cybersecurity expertise and how that expertise supports effective oversight. Organizations must define cybersecurity expertise standards and evaluate director qualifications against those criteria, potentially identifying expertise gaps that require board composition changes or enhanced director education programs.
This requirement has accelerated the search for board directors with cybersecurity backgrounds and increased demand for cybersecurity education programs for existing directors. Organizations are investing in board training initiatives to ensure directors can effectively evaluate cybersecurity risks and oversee management’s risk mitigation strategies.
Implementation Timeline and Compliance
For companies with public floats exceeding $250 million, Form 8-K incident disclosure obligations took effect on December 18, 2023. Cybersecurity risk management, strategy, and governance disclosures must be included in annual reports for fiscal years ending on or after December 15, 2023.
Smaller reporting companies have additional time to implement these requirements, but the disclosure obligations ultimately apply to all public companies. This phased implementation allows organizations to learn from early adopters and refine their governance and reporting processes based on emerging best practices.
Essential Components of Board Cybersecurity Reports
Effective cybersecurity board reporting requires standardized components that provide directors with comprehensive visibility into the organization’s security posture, risk exposure, and program performance. These components must balance technical accuracy with business relevance, ensuring directors receive actionable intelligence that supports informed governance decisions.
Executive Summary and Risk Assessment
Every board cybersecurity report should begin with a concise executive summary that highlights the most critical information requiring board attention. This summary should present the organization’s current risk level using simple, color-coded indicators (green, yellow, red) and include brief explanations of any significant changes since the previous report.
The risk assessment section must translate technical vulnerabilities into business impact scenarios. Rather than listing specific technical findings, effective reports describe potential consequences in terms of operational disruption, financial loss, regulatory exposure, and reputational damage. This approach enables directors to understand cybersecurity risks within the broader context of enterprise risk management.
Security Program Performance Metrics
Board reports must include key performance indicators that demonstrate security program effectiveness over time. These metrics should focus on outcomes rather than activities, showing how security investments translate into risk reduction and business value creation.
Essential performance metrics include:
Risk Reduction Indicators: Trends in critical vulnerability exposure, mean time to detect security incidents, and mean time to respond to threats. These metrics demonstrate the organization’s improving ability to identify and address security risks before they impact business operations.
Program Maturity Assessments: Regular evaluation of security program maturity using established frameworks like NIST or ISO 27001. Board reports should show progress toward specific maturity targets and highlight areas requiring additional investment or attention.
Business Impact Metrics: Measures that directly relate to business outcomes, such as security-related business disruption hours, customer data protection effectiveness, and regulatory compliance status. These metrics help directors understand how cybersecurity performance affects broader business objectives.
Financial Performance and Budget Analysis
Directors require clear visibility into cybersecurity spending effectiveness and return on investment. Board reports should include detailed analysis of security budget performance, including actual spending versus planned investments and the business value generated by security initiatives.
Financial reporting should distinguish between operational security expenses (ongoing monitoring, staff, tools) and strategic security investments (new capabilities, infrastructure upgrades, compliance initiatives). This categorization helps directors understand how security spending supports both immediate risk management and long-term strategic objectives.
Cost avoidance calculations provide valuable context for security investments. Reports should quantify the financial impact of incidents prevented, regulatory penalties avoided, and business disruption minimized through effective security measures. These calculations help directors evaluate security ROI using familiar financial frameworks.
Regulatory Compliance Status
Given the expanding regulatory landscape for cybersecurity, board reports must provide comprehensive compliance status updates across all applicable frameworks. This includes traditional compliance requirements (HIPAA, PCI DSS, SOX) as well as emerging regulations (state privacy laws, sector-specific requirements).
Organizations pursuing SOC 2 compliance require specialized reporting frameworks that demonstrate control effectiveness to auditors and stakeholders. Compliance reporting should highlight any gaps requiring immediate attention, planned remediation activities, and timeline for achieving full compliance. Directors need to understand potential regulatory exposure and the resources required to maintain compliance as requirements evolve.
Strategic Alignment and Future Planning
Effective board reports demonstrate how cybersecurity strategy aligns with broader business objectives and supports strategic initiatives. This section should explain how security investments enable business growth, facilitate digital transformation, and support market expansion plans.
Future planning components should address emerging threats, technology changes, and regulatory developments that may require strategic adjustments. Directors need visibility into how the security program will evolve to support changing business requirements and address new risk scenarios.
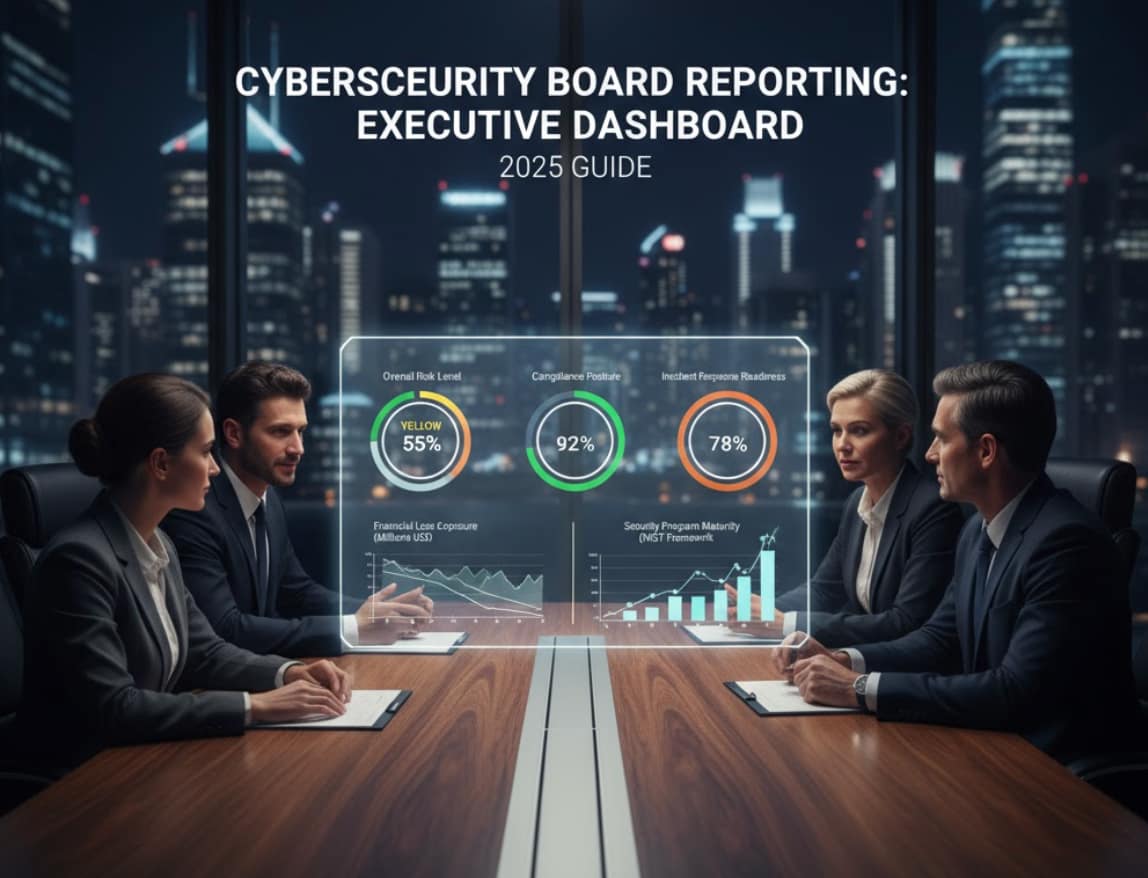
Executive Dashboard Framework
Modern cybersecurity board reporting leverages executive dashboards that provide real-time visibility into security posture through intuitive visualizations and key performance indicators. These dashboards must balance comprehensive coverage with executive-friendly presentation, enabling directors to quickly assess organizational risk and security program effectiveness.

Dashboard Design Principles
Executive cybersecurity dashboards should follow established design principles that prioritize clarity, relevance, and actionability. The dashboard must present information hierarchically, with the most critical metrics prominently displayed and supporting details available through drill-down capabilities.
Visual design should use consistent color coding throughout all dashboard components. Red indicators signal critical issues requiring immediate board attention, yellow indicates areas of concern requiring monitoring and planned action, and green represents satisfactory performance within acceptable risk parameters. This traffic light approach provides immediate visual context for risk assessment.
Information architecture should group related metrics logically, with sections dedicated to risk assessment, program performance, compliance status, and financial metrics. Each section should include both current status and trend indicators, enabling directors to understand both current state and trajectory.
Key Performance Indicator Selection
Dashboard KPIs must translate technical security metrics into business-relevant indicators that support governance decision-making. Effective KPI selection requires collaboration between security teams and business leadership to identify metrics that accurately reflect organizational risk while remaining understandable to non-technical directors.
Risk Exposure Metrics: Current threat level based on external intelligence, critical vulnerability exposure, and security control effectiveness. These metrics should be presented as relative risk scores rather than absolute technical measurements, enabling directors to understand risk in business context.
Operational Performance Indicators: Security program effectiveness measured through incident response times, security awareness training completion rates, and third-party risk assessment completion. These metrics demonstrate security program execution and identify areas requiring management attention.
Financial Impact Measures: Security spending as percentage of IT budget, cost per security incident, and security ROI calculations. Financial metrics enable directors to evaluate security program efficiency and justify continued investment in cybersecurity capabilities.
Compliance and Governance Metrics: Regulatory compliance scores, policy compliance rates, and audit finding resolution status. These metrics provide visibility into regulatory risk and demonstrate management’s commitment to maintaining compliance standards.
Real-Time Monitoring Capabilities
Modern executive dashboards provide real-time visibility into critical security events and program performance. Real-time capabilities enable boards to monitor security posture between formal reporting periods and receive immediate notification of significant incidents or changes in risk exposure.
Alert mechanisms should be carefully calibrated to ensure board members receive notification of truly significant events without overwhelming them with routine operational information. Threshold settings should distinguish between information requiring immediate board attention and updates that can wait for regular reporting cycles.
Integration with security monitoring systems enables automatic dashboard updates as new information becomes available. This integration ensures dashboard accuracy and reduces manual reporting overhead that can delay critical communications.
Mobile Accessibility and User Experience
Executive dashboards must be accessible across multiple devices and platforms, enabling directors to monitor security posture regardless of location or device. Mobile-optimized interfaces ensure directors can access critical information during travel or outside normal business hours.
User experience design should minimize cognitive load through clear information hierarchy, consistent navigation patterns, and intuitive interaction design. Directors should be able to access needed information quickly without extensive training or technical expertise.
Customization capabilities allow individual directors to configure dashboard views based on their specific interests and responsibilities. For example, audit committee members may prioritize compliance metrics, while the full board may focus on strategic risk indicators.
Key Cybersecurity Metrics for Directors
Effective cybersecurity board reporting requires carefully selected metrics that translate technical security performance into business-relevant indicators. These metrics must provide directors with actionable intelligence while avoiding technical complexity that obscures business implications.
Risk-Based Security Metrics
Quantified Risk Exposure: Present cybersecurity risk in financial terms using established risk quantification methodologies. Express potential loss exposure as dollar amounts based on threat likelihood and business impact analysis. This approach enables directors to evaluate cybersecurity risk using familiar financial frameworks and compare security investments against other business risks.
Comprehensive security risk assessments provide the foundation for quantifying organizational risk exposure in financial terms. Risk Trend Analysis: Track risk exposure changes over time to demonstrate security program effectiveness. Show how security investments and controls implementation reduce organizational risk exposure. Include trend lines showing progress toward established risk tolerance levels and highlight areas where risk exposure exceeds acceptable thresholds.
Threat Intelligence Integration: Provide context for organizational risk based on current threat landscape and industry-specific targeting trends. Translate threat intelligence into business impact scenarios that help directors understand how external threat changes affect organizational risk posture.
Operational Performance Indicators
Mean Time to Detect (MTTD): Track the average time between security incident occurrence and detection. Present this metric in business context, explaining how faster detection reduces potential damage and business disruption. Show improvement trends and benchmark performance against industry standards.
Mean Time to Respond (MTTR): Measure average time from incident detection to initial response. Explain how faster response times minimize business impact and demonstrate security team effectiveness. Include analysis of response time factors and improvement initiatives.
Security Control Effectiveness: Evaluate how well security controls prevent, detect, and respond to threats. Present effectiveness as percentage of threats successfully blocked or contained, with trend analysis showing improvement over time. Include root cause analysis for control failures and planned improvements.
Employee Security Awareness: Track security training completion rates, phishing simulation results, and security policy compliance. Present these metrics as indicators of human risk factors and organizational security culture maturity. Show correlation between awareness training and actual security incident reduction.
Financial and Business Impact Metrics
Security ROI Analysis: Calculate return on investment for major security initiatives using prevented loss, operational efficiency gains, and business enablement benefits. Present ROI calculations using standard financial analysis methods familiar to board members.
Cost Per Incident: Track total cost of security incidents including response, recovery, business disruption, and regulatory penalties. Show how this metric trends downward as security program maturity improves and response capabilities develop.
Business Continuity Metrics: Measure actual business disruption from security incidents, including downtime duration, affected systems, and customer impact. These metrics demonstrate security program business value through reduced operational disruption.
Compliance Cost Efficiency: Track spending required to maintain regulatory compliance and compare efficiency across different compliance frameworks. Show how integrated compliance approaches reduce overall compliance costs.
Strategic Performance Indicators
Security Program Maturity: Use established frameworks to assess and report security program maturity levels. Show progress toward target maturity levels and identify gaps requiring additional investment or focus.
Third-Party Risk Management: Track security assessment completion for critical vendors, security contract compliance, and supply chain risk exposure. Present vendor risk as business continuity risk rather than technical security concern.
Digital Transformation Enablement: Demonstrate how security capabilities enable or constrain business initiatives like cloud adoption, digital customer experiences, and new technology implementation. Show security as business enabler rather than impediment.
Regulatory and Compliance Metrics
Compliance Framework Status: Provide overall compliance scores for applicable regulations with detailed gap analysis and remediation timelines. Use visual indicators to show compliance trajectory and highlight areas requiring immediate attention.
Audit and Assessment Results: Summarize findings from internal audits, external assessments, and regulatory examinations. Present findings in business risk context and show management response and remediation progress.
Regulatory Change Impact: Track new regulatory requirements and their implementation status. Provide timeline and resource requirements for achieving compliance with emerging regulations.
Risk Communication and Financial Quantification
Effective cybersecurity board reporting requires translating technical risk assessments into financial terms that enable directors to make informed resource allocation decisions. This translation process must maintain technical accuracy while presenting risk information in business context that supports governance responsibilities.
Cyber Risk Quantification Methodologies
Modern cyber risk quantification uses established frameworks like Factor Analysis of Information Risk (FAIR) to express security threats in financial terms. These methodologies analyze threat likelihood, vulnerability exposure, and business impact to calculate probable loss ranges for specific risk scenarios.
Quantification processes begin with asset valuation and threat modeling to establish baseline loss potential. Analysis includes direct costs (incident response, system recovery, regulatory penalties) and indirect costs (business disruption, customer loss, reputational damage). The resulting risk calculations provide dollar-denominated risk exposure that directors can evaluate against other business risks.
Risk quantification must include uncertainty ranges rather than point estimates, acknowledging the inherent uncertainty in threat likelihood and impact assessment. Present risk ranges using confidence intervals that communicate both expected loss and potential variation. This approach provides realistic expectations while avoiding false precision that undermines credibility.
Business Impact Scenario Development
Effective risk communication uses specific business impact scenarios that illustrate how cyber threats translate into operational and financial consequences. These scenarios should reflect the organization’s actual business model, critical assets, and operational dependencies.
Revenue Impact Scenarios: Describe how different types of cyber incidents affect revenue generation through system downtime, customer data compromise, or service delivery disruption. Quantify revenue impact based on historical business data and recovery timeline estimates.
Operational Disruption Analysis: Model business process interruption from various cyber incident types, including manufacturing shutdown, financial system unavailability, or customer service system compromise. Include productivity loss, recovery costs, and customer satisfaction impact.
Regulatory and Legal Exposure: Quantify potential penalties, investigation costs, and litigation exposure from data breaches or compliance violations. Include both direct regulatory penalties and indirect costs from legal proceedings and regulatory oversight.
Reputational Damage Assessment: Estimate customer loss, market share reduction, and brand value impact from high-profile security incidents. Use industry case studies and academic research to support reputational impact projections.
Understanding how data breaches impact brand trust and loyalty helps directors evaluate reputational damage scenarios beyond direct financial costs, enabling more comprehensive risk assessments for board decision-making.
Cost-Benefit Analysis Framework
Board reporting must demonstrate security investment value through comprehensive cost-benefit analysis that compares security spending against risk reduction and business value creation. This analysis framework enables directors to evaluate security investments using standard capital allocation criteria.
Prevention Cost Analysis: Calculate total cost of security controls including technology, personnel, training, and compliance overhead. Break down costs by control category to show investment allocation across different risk mitigation approaches.
Avoided Loss Calculations: Quantify financial benefits from incidents prevented, compliance penalties avoided, and business disruption minimized. Use historical incident data and industry benchmarks to estimate prevented loss value.
Business Enablement Benefits: Identify revenue opportunities and operational efficiencies enabled by security capabilities. Include customer trust benefits, partnership opportunities, and market access improvements from demonstrated security competence.
Risk Transfer Evaluation: Analyze cyber insurance costs and coverage against self-insurance alternatives. Present insurance as one component of comprehensive risk management strategy rather than complete risk transfer solution.
Incident Reporting to the Board
Cybersecurity incident reporting to the board requires structured processes that provide timely, accurate, and actionable information while maintaining appropriate confidentiality during active investigations. Effective incident reporting balances transparency with operational security requirements and legal considerations.

Incident Classification and Escalation
Board-level incident reporting requires clear classification criteria that distinguish incidents requiring immediate board notification from routine security events handled through normal operational processes. Classification systems should focus on business impact rather than technical characteristics.
Critical Incidents: Require immediate board notification within 24 hours and include incidents with potential material business impact, regulatory reporting requirements, or significant customer data exposure. Critical incident reports should provide preliminary impact assessment and initial response actions.
Significant Incidents: Warrant board notification within 72 hours for incidents with moderate business impact, limited data exposure, or potential compliance implications. These reports can include more detailed analysis and initial lessons learned.
Routine Security Events: Handled through normal operational processes with summary reporting in regular board reports. Include trend analysis and pattern identification but avoid overwhelming board with operational details.
Classification criteria should align with SEC materiality guidelines to ensure consistent evaluation of disclosure requirements. Regular review and updating of classification criteria ensures continued relevance as business and threat landscapes evolve.
Initial Incident Reporting
Initial incident reports to the board must provide essential information while acknowledging the preliminary nature of early assessments. These reports should focus on known facts, immediate response actions, and potential business implications rather than detailed technical analysis.
Effective incident response services ensure boards receive timely, accurate information during crisis situations while maintaining appropriate confidentiality during active investigations.
Incident Overview: Describe what happened, when it was discovered, and what systems or data may be affected. Use business terminology rather than technical jargon and focus on potential business impact rather than technical details.
Immediate Response Actions: Summarize containment measures, investigative steps, and stakeholder notifications. Explain how the incident response team is managing the situation and what additional resources may be required.
Preliminary Impact Assessment: Provide initial estimates of affected customers, data exposure, system downtime, and potential business disruption. Acknowledge uncertainty in early assessments while providing best available information.
Regulatory and Legal Considerations: Identify potential reporting requirements, legal exposure, and stakeholder notification obligations. Include timeline for regulatory filings and external communications.
Ongoing Investigation Updates
Complex incidents require regular updates as investigation proceeds and impact becomes clearer. Update frequency should match incident severity and board information needs while avoiding information overload.
Investigation updates should track key metrics including affected customer counts, data exposure scope, system recovery progress, and cost accumulation. Present information consistently across updates to enable trend tracking and impact assessment.
Include lessons learned development and corrective action planning in ongoing updates. Show how investigation findings inform security program improvements and future incident prevention.
Post-Incident Analysis and Reporting
Comprehensive post-incident reports provide detailed analysis of incident causes, response effectiveness, business impact, and improvement opportunities. These reports serve both governance and operational improvement purposes.
Root Cause Analysis: Explain incident causes in business context, including process failures, control gaps, and decision points that contributed to incident occurrence or impact. Focus on systemic issues rather than individual blame.
Response Effectiveness Assessment: Evaluate incident response performance including detection time, response coordination, communication effectiveness, and recovery speed. Identify successful practices and improvement opportunities.
Financial Impact Analysis: Provide comprehensive cost analysis including direct response costs, business disruption impact, regulatory penalties, and recovery expenses. Include comparison to prevented loss through effective response.
Program Improvement Recommendations: Present specific actions to prevent similar incidents and improve response capabilities. Include timeline, resource requirements, and expected risk reduction benefits for each recommendation.
Compliance and Regulatory Reporting
Cybersecurity compliance reporting to the board must provide comprehensive visibility into regulatory adherence while demonstrating management’s commitment to maintaining compliance standards. This reporting becomes increasingly critical as regulatory requirements expand and penalties for non-compliance escalate.
Multi-Framework Compliance Tracking
Organizations typically must comply with multiple regulatory frameworks simultaneously, requiring integrated reporting that shows compliance status across all applicable requirements. Board reports should provide unified compliance dashboards that highlight overall compliance posture and framework-specific details.
Organizations often need guidance on preparing for cybersecurity audits across multiple regulatory frameworks simultaneously, ensuring comprehensive readiness for compliance assessments.
Comprehensive Compliance Score: Present overall compliance status using weighted scoring that reflects the relative importance and complexity of different regulatory requirements. Show trend analysis demonstrating compliance trajectory and highlight areas requiring immediate attention.
Framework-Specific Status: Provide detailed compliance status for major frameworks including HIPAA, PCI DSS, SOX, GDPR, and industry-specific regulations. Use consistent scoring methodology across frameworks to enable comparative analysis.
Gap Analysis and Remediation: Identify specific compliance gaps with detailed remediation plans, timelines, and resource requirements. Show progress on gap closure and highlight any delays or resource constraints affecting compliance timeline.
Regulatory Change Management: Track new regulatory requirements and their implementation status. Provide impact analysis for emerging regulations and timeline for achieving compliance with new requirements.
Audit and Assessment Results
External audits and compliance assessments provide independent validation of security controls and compliance status. Board reporting should synthesize audit results and present findings in business risk context.
Audit Finding Categorization: Present audit findings grouped by risk level and business impact rather than technical control categories. Explain how findings affect business operations and compliance status rather than focusing on technical details.
Management Response Tracking: Show management’s response to audit findings including corrective action plans, implementation timelines, and progress updates. Demonstrate management commitment to addressing identified deficiencies.
Trend Analysis: Track audit results over time to show compliance program maturity and continuous improvement. Compare current results to previous assessments and industry benchmarks.
Cost-Benefit Analysis: Evaluate audit and assessment costs against compliance risk reduction and business value creation. Show how assessment investments contribute to overall risk management strategy.
Regulatory Relationship Management
Effective compliance reporting includes updates on regulatory relationships, examination results, and regulatory communication. This information helps boards understand regulatory risk and oversight intensity.
Regulatory Examination Status: Provide updates on ongoing regulatory examinations including scope, timeline, and preliminary findings. Explain examination process and expected outcomes for board understanding.
Regulatory Communication: Summarize significant communications with regulators including guidance updates, enforcement actions, and policy changes affecting the organization. Explain implications for compliance strategy and resource requirements.
Industry Regulatory Trends: Provide context on regulatory developments affecting the industry including new requirements, enforcement priorities, and regulatory focus areas. Show how the organization’s compliance strategy addresses emerging regulatory expectations.
Compliance Program Effectiveness
Board reports should demonstrate compliance program effectiveness through metrics that show how compliance activities reduce regulatory risk and support business objectives.
Compliance Cost Efficiency: Track compliance spending per regulatory framework and compare efficiency across different compliance approaches. Show how integrated compliance programs reduce overall compliance costs.
Risk Reduction Metrics: Quantify regulatory risk reduction through compliance program effectiveness measures. Include metrics on control effectiveness, policy compliance rates, and training completion.
Business Enablement: Demonstrate how effective compliance enables business opportunities including customer trust, partnership opportunities, and market access. Show compliance as business enabler rather than cost center.
Board Reporting Templates and Best Practices
Standardized board reporting templates ensure consistent, comprehensive cybersecurity communication while reducing preparation time and improving information quality. These templates must balance thoroughness with executive accessibility, providing directors with essential information in digestible formats.
Executive Summary Template
Every cybersecurity board report should begin with a concise executive summary that highlights critical information requiring board attention. This summary must distill complex security information into key insights and recommendations.
Managed security services provide the operational data and continuous monitoring that powers real-time executive dashboards, enabling accurate and timely board reporting.
Risk Level Assessment: Present current organizational risk level using clear visual indicators (red, yellow, green) with brief explanation of any changes since the previous report. Include specific actions required from the board if risk level is elevated.
Critical Issues: Highlight immediate security concerns requiring board awareness or action. Limit to 2-3 most significant issues with clear business impact explanation and recommended board response.
Program Performance: Summarize security program effectiveness using 3-4 key metrics that demonstrate risk reduction and business value creation. Show trend direction and comparison to established targets.
Financial Summary: Provide budget performance overview including spending variance analysis and significant cost changes. Include brief explanation of any budget adjustments or additional resource requirements.
Regulatory Status: Summarize compliance posture across applicable frameworks with specific attention to any regulatory changes or emerging requirements affecting the organization.
Detailed Metrics Dashboard
The detailed metrics section provides comprehensive security program performance data supporting the executive summary. This section should use consistent formatting and presentation across reporting periods.
Risk Metrics Table: Present key risk indicators in tabular format showing current value, previous period comparison, trend direction, and target performance. Include brief explanations for significant variances or concerning trends.
Operational Performance Charts: Use visual charts to show security program effectiveness trends including incident response times, vulnerability management performance, and security training completion rates.
Financial Performance Analysis: Provide detailed budget analysis including spending by category, cost per security metric, and return on investment calculations for major security initiatives.
Compliance Scorecard: Present compliance status across applicable frameworks using consistent scoring methodology with specific gap identification and remediation timeline.
Best Practices for Report Preparation
Collaboration Requirements: Effective board reporting requires collaboration between security, risk, legal, and business teams to ensure comprehensive, accurate reporting. Establish clear roles and responsibilities for report preparation and review.
Data Quality Assurance: Implement data validation processes to ensure report accuracy and consistency. Use automated data collection where possible to reduce manual errors and improve reporting efficiency.
Executive Review Process: Require executive review and approval before board presentation to ensure report accuracy and appropriate business context. Include legal review for regulatory compliance and disclosure considerations.
Board Member Preparation: Provide board members with background materials and metric definitions to enhance report comprehension and discussion quality. Consider pre-meeting briefings for complex topics.
Follow-up Documentation: Document board discussions, decisions, and action items from cybersecurity reporting sessions. Ensure appropriate follow-up on board directives and decision implementation.
Common Reporting Challenges and Solutions
Cybersecurity board reporting faces recurring challenges that can undermine communication effectiveness and board understanding. Identifying these challenges and implementing proven solutions improves reporting quality and board engagement with cybersecurity governance.
Technical Complexity Translation
Challenge: Security teams naturally think in technical terms that don’t translate well to board-level discussions. Directors may lack technical background to understand complex security concepts, creating communication barriers that impede effective governance.
Many organizations find that GRC platforms fail without proper guidance from experienced cybersecurity leadership, highlighting the importance of executive-level security expertise in board communication.
Solution: Develop standardized translation frameworks that convert technical metrics into business impact scenarios. Use analogies and business examples to explain security concepts. Create glossaries of security terms with business definitions. Train security staff in business communication and consider appointing security liaisons with both technical and business expertise.
Implementation: Establish regular training sessions for security staff on business communication. Develop template language for common security concepts. Create executive briefing materials that provide context for technical topics before board meetings.
Information Overload Prevention
Challenge: Boards can become overwhelmed with excessive security detail that obscures key insights and decision points. Too much information can be as problematic as too little, leading to decision paralysis or important issues being overlooked.
Solution: Implement information hierarchy principles that present critical information first with supporting detail available on request. Use executive summary formats that highlight key decisions required from the board. Limit routine reports to predetermined page counts and metric sets.
Implementation: Develop report templates with mandatory executive summaries. Establish clear criteria for information requiring board attention versus operational details. Use appendices for supporting technical information that doesn’t require board action.
Inconsistent Reporting Frequency
Challenge: Ad hoc reporting schedules can lead to information gaps during critical periods or information overload during routine periods. Inconsistent reporting makes trend analysis difficult and may miss time-sensitive issues.
Solution: Establish standardized reporting calendars aligned with board meeting schedules and business cycles. Implement escalation procedures for urgent issues requiring immediate board notification outside regular reporting cycles.
Implementation: Create annual reporting calendars with regular board reports, annual strategic reviews, and incident reporting procedures. Establish clear escalation criteria and communication protocols for urgent issues.
Building an Effective Board Reporting Program
Establishing comprehensive cybersecurity board reporting requires systematic program development that aligns reporting processes with governance requirements and business objectives. Successful implementation demands collaboration across multiple organizational functions and sustained commitment to reporting quality improvement.
Program Design and Planning
Effective board reporting programs begin with comprehensive planning that defines reporting objectives, stakeholder requirements, and success criteria. This planning process must align cybersecurity reporting with broader governance processes and regulatory requirements.
Understanding what to expect during vCISO implementation helps organizations plan realistic timelines for board reporting program development and set appropriate expectations for governance improvement.
Stakeholder Requirements Analysis: Conduct detailed analysis of board information needs including preferred reporting formats, metric priorities, and decision support requirements. Interview board members individually to understand specific interests and expertise levels.
Regulatory Mapping: Identify all applicable regulatory reporting requirements and ensure board reporting programs address compliance obligations. Map regulatory requirements to board reporting components to ensure comprehensive coverage.
Resource Planning: Assess resource requirements for reporting program including staff time, technology infrastructure, and external support needs. Develop realistic implementation timelines that account for competing priorities and resource constraints.
Governance Integration: Align cybersecurity reporting with existing board governance processes including committee structures, meeting schedules, and decision-making frameworks. Ensure cybersecurity reporting enhances rather than duplicates existing governance activities.
Technology Infrastructure Development
Modern board reporting requires technology infrastructure that automates data collection, enables real-time reporting, and provides executive-friendly presentation capabilities.
Data Integration Platforms: Implement platforms that integrate data from multiple security tools, business systems, and external sources. Automated data integration reduces manual reporting overhead and improves data accuracy and timeliness.
Dashboard and Visualization Tools: Deploy executive dashboard solutions that provide real-time visibility into security metrics with drill-down capabilities for detailed analysis. Ensure mobile accessibility for directors who need access outside normal business hours.
Reporting Automation: Automate routine report generation and distribution to reduce manual effort and ensure consistent reporting schedules. Implement alert mechanisms for critical issues requiring immediate board notification.
Data Quality Controls: Establish data validation and quality assurance processes to ensure report accuracy and reliability. Implement audit trails and change controls for reporting data and calculations.
Success Measurement and Validation
Effective board reporting programs require measurement criteria that demonstrate value creation and continuous improvement. Success metrics should focus on governance effectiveness rather than reporting activity.
Board Engagement Metrics: Measure board engagement with cybersecurity topics through meeting discussion time, question frequency, and decision quality. Track board confidence in cybersecurity oversight capabilities.
Decision Support Effectiveness: Evaluate how board reporting supports governance decisions including resource allocation, strategic planning, and risk management. Track correlation between reporting quality and decision outcomes.
Regulatory Compliance: Monitor compliance with regulatory reporting requirements and board oversight obligations. Track audit findings and regulatory feedback related to board governance effectiveness.
Business Value Creation: Assess how effective board oversight contributes to business value creation through risk reduction, business enablement, and stakeholder confidence. Connect governance effectiveness to business outcomes.
Conclusion
Cybersecurity board reporting has evolved from optional IT updates to essential governance infrastructure supporting strategic decision-making and regulatory compliance. As cyber threats continue escalating and regulatory requirements expand, boards require sophisticated reporting frameworks that translate technical security performance into business-relevant intelligence.
Effective cybersecurity board reporting balances comprehensiveness with accessibility, providing directors with actionable insights while avoiding technical complexity that impedes governance effectiveness. Success requires systematic program development including stakeholder analysis, technology infrastructure, staff development, and continuous improvement processes.
The investment in comprehensive board reporting capabilities pays dividends through enhanced governance effectiveness, improved regulatory compliance, and better alignment between cybersecurity strategy and business objectives. Organizations that implement robust board reporting programs position themselves for sustained success in an increasingly complex threat and regulatory environment.
For organizations seeking to enhance their cybersecurity governance capabilities, professional guidance can accelerate program development and ensure best practice implementation. Virtual CISO services provide executive-level security leadership that includes comprehensive board reporting program development and ongoing governance support.
Ready to enhance your cybersecurity board reporting? Schedule a consultation to discuss how comprehensive board reporting frameworks can strengthen your organization’s governance capabilities and regulatory compliance posture.

Jeff Sowell is a cybersecurity leader with over 20 years of experience in IT and security roles at Fortune 500 companies. He has held key positions such as VP, CISO, and CPSO, serving as Head of Product Security at Ericsson North America. Jeff holds an M.S. in Computer Information Systems (Security) from Boston University and industry-recognized certifications including CISSP, CISM, and ISO 27001 Lead Implementor.
Related services