
How to Add a Cybersecurity Practice to Your MSP Without Hiring a CISO
Every MSP owner has the same problem. Cybersecurity is in every renewal conversation, but the delivery capability isn't there. Here are the three paths forward, with real numbers.
Expert cybersecurity insights, threat intelligence, and compliance guides

Every MSP owner has the same problem. Cybersecurity is in every renewal conversation, but the delivery capability isn't there. Here are the three paths forward, with real numbers.
275 million Americans had their PHI exposed in 2024 — a new HIPAA breach record. Here's what the OCR data shows about ransomware, business associates, and what mid-market healthcare must do next.
A full-time CISO in Dallas-Fort Worth costs $200K-$400K before benefits. Here is a direct comparison of building an internal security team vs. using a virtual CISO for DFW mid-market companies.
The stretch of I-35 between Austin and Dallas has almost no dedicated cybersecurity firms. Central Texas businesses are left choosing between distant metro providers or local IT shops adding security to their menu.
Killeen businesses supporting Fort Cavazos face growing cybersecurity requirements. CMMC compliance, CUI protection, and security programs built for the defense supply chain.
Temple, TX businesses face unique cybersecurity challenges driven by healthcare, manufacturing, and proximity to Fort Cavazos. Here is what Central Texas organizations need to know.
The SEC cybersecurity disclosure rules are reshaping how companies report breaches. Even if you are not publicly traded, these rules affect your business. Here is what mid-market organizations need to do now.
MSSPs and vCISOs need GRC tools built for multi-client operations — not enterprise platforms shoehorned into service-provider workflows. Here's what to look for in 2026.
Your employees are already using AI tools you don't know about. Shadow AI is the fastest-growing security risk for mid-market companies.
Most companies are adopting AI tools without formal vendor assessment. Here's the framework and specific questions your security leader should be asking.
Most mid-market companies don't have dedicated AI risk teams. Here's how to build an effective AI risk management program with the resources you already have.
The EU AI Act applies to US companies that serve European markets. Here's what mid-market leaders need to know about compliance obligations, timelines, and risk.
A practical, step-by-step AI governance checklist built for mid-market companies that need to manage AI risk without a dedicated governance team.

Many organizations confuse penetration testing with vulnerability scanning — a costly mistake. Learn the key differences, when each is appropriate, and how to build a security testing strategy that delivers real results.

San Antonio's military community needs cybersecurity services that meet defense requirements. Managed security for contractors supporting Joint Base San Antonio and beyond.

D.C.-area government contractors need cybersecurity architecture that satisfies federal compliance requirements while remaining operationally practical.

McLean-area technology companies serving federal agencies need FedRAMP authorization. Navigate the complex authorization process with expert compliance guidance.

Bay Area AI companies face unique security challenges: protecting training data, securing ML pipelines, and meeting emerging AI governance requirements. Here's what you need to know.

Bay Area SaaS companies need Fortune 500-grade security leadership to close enterprise deals, but can't justify a $400K CISO hire. Virtual CISO services bridge the gap.

San Diego biotech companies hold some of the most valuable intellectual property in the world. Learn how to protect research data, clinical trials, and trade secrets from cyber threats.

San Diego defense contractors must achieve CMMC compliance to maintain DoD contracts. Learn the specific controls, timelines, and strategies for certification success.

Cleveland's interconnected supply chains create cascading cyber risk. Learn how to assess vendor security, meet compliance requirements, and protect your organization from third-party breaches.

Cleveland manufacturers face growing cyber threats targeting operational technology. Learn how to protect SCADA systems, PLCs, and production lines from attacks that cause real-world damage.
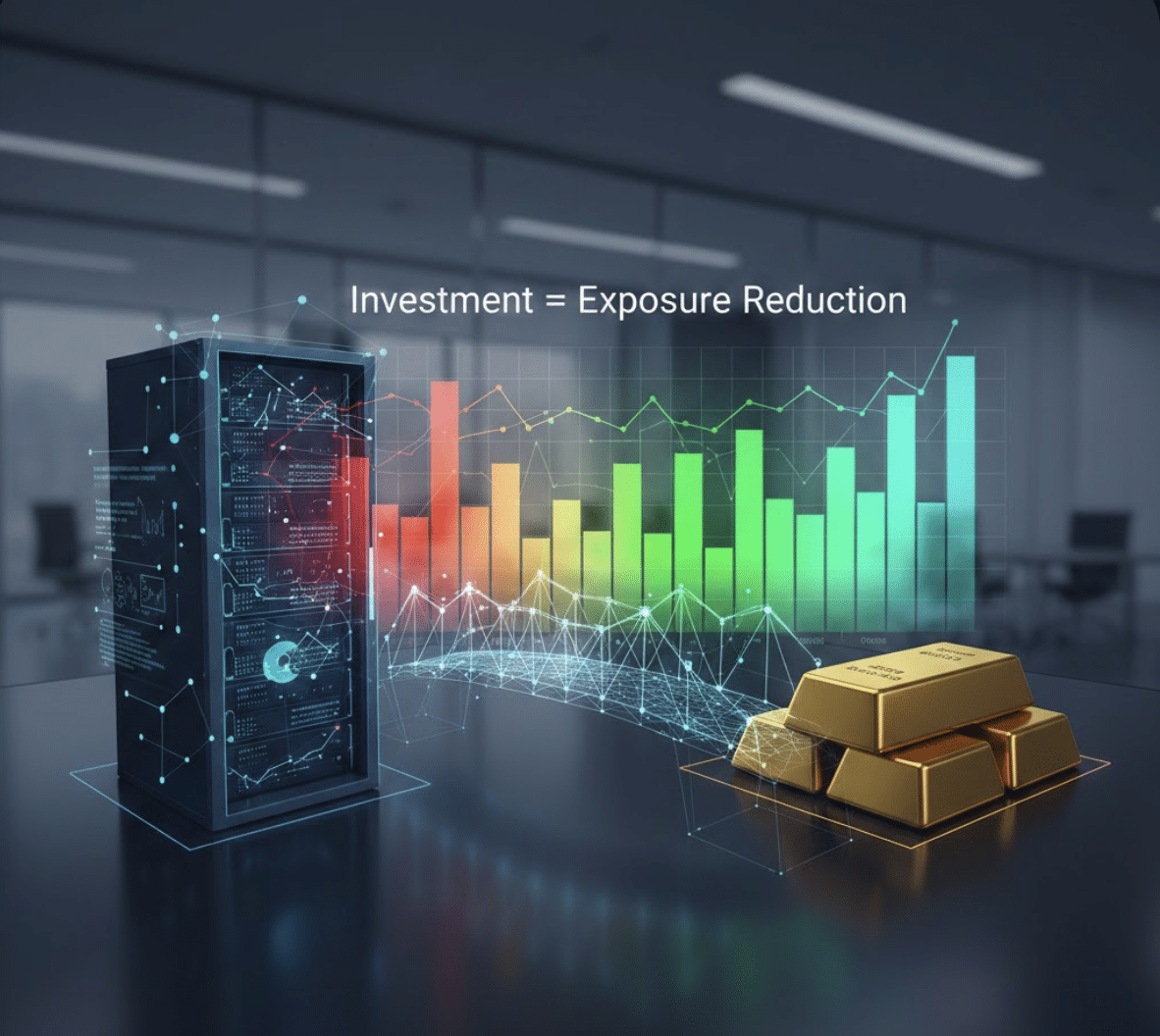
When the CFO asks "why does cybersecurity cost this much?" — you need more than a vendor quote. You need a budget that speaks the language of business risk, not technical jargon. This guide walks you through exactly how to build a cybersecurity budget your finance team will actually approve, complete with allocation benchmarks, a …
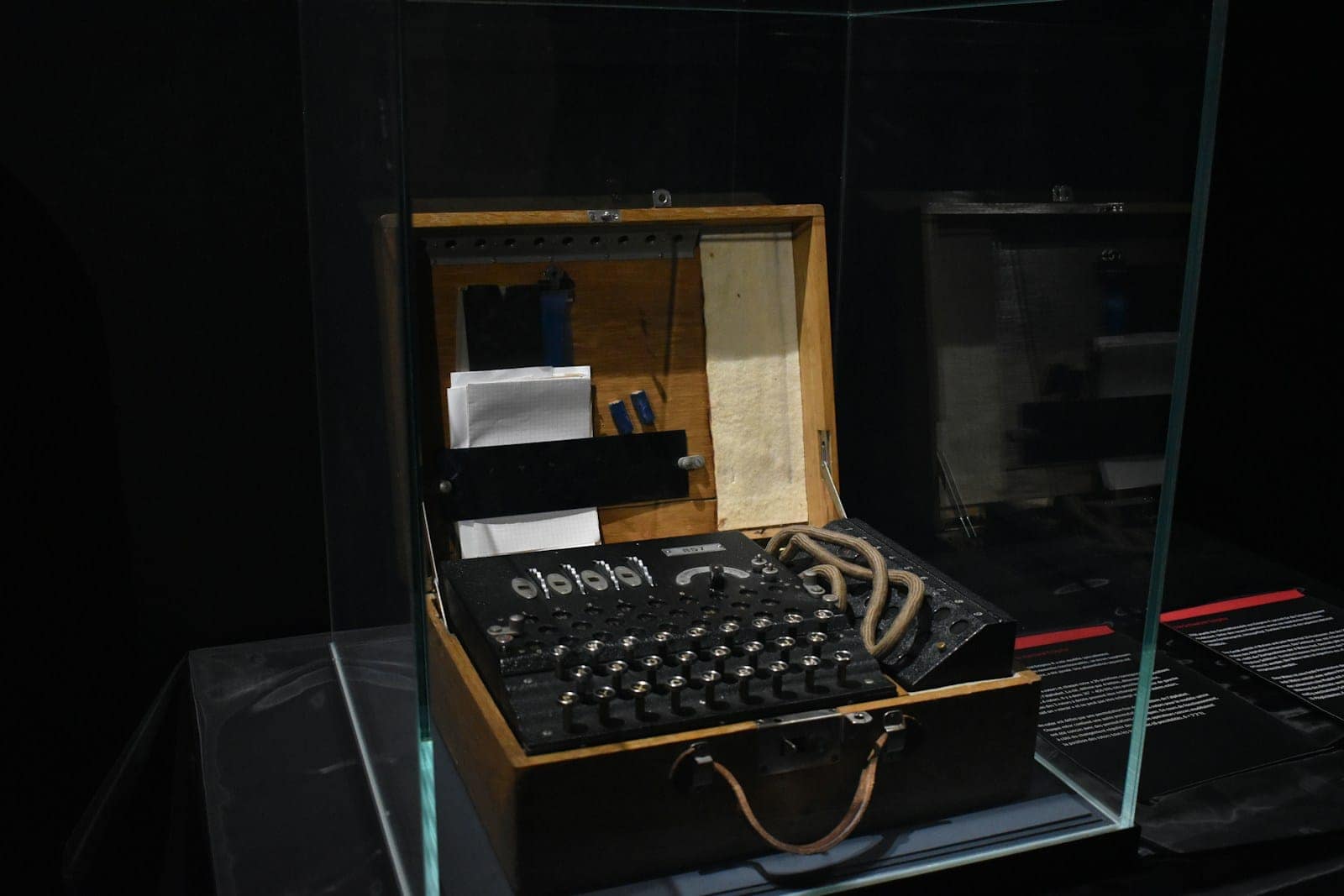
When Anthropic launched Claude Code Security, public cybersecurity stocks sold off hard. CrowdStrike and Cloudflare fell roughly 8%. Okta and SailPoint dropped around 10%. Israel's JFrog shed nearly 25% in a single session. The easy headline wrote itself: AI just killed cybersecurity. That narrative is wrong, but it is pointing at something real that every …

The legal profession faces a cybersecurity crisis that threatens the very foundation of attorney-client privilege. With 29% of law firms reporting security breaches according to the 2023 American Bar Association Legal Technology Survey, the legal industry can no longer treat cybersecurity as an optional consideration—it's now a fundamental requirement for maintaining client trust and professional …

Scale-stage security expertise for Seattle's venture-backed technology companies built on Amazon Web Services infrastructure Quick Answer Seattle tech startups need specialized virtual CISO expertise that understands both rapid scaling challenges and AWS-native architectures. Unlike traditional security leadership, virtual CISOs serving Seattle's tech ecosystem must navigate cloud-first security frameworks, venture funding security requirements, and the unique …

Introduction: The Hidden Security Crisis in AI-Assisted Development Development firms across the United States are rapidly adopting AI coding tools like GitHub Copilot, ChatGPT Code Interpreter, and Amazon CodeWhisperer to accelerate software development. While these tools deliver impressive productivity gains, they also introduce a critical security challenge that most firms aren't adequately addressing: GitHub Copilot …

A devastating pattern emerged across America this week: critical government services grinding to halt under cyberattacks while federal cybersecurity support evaporates. Kaufman County, Texas discovered a cyberattack Monday that forced county officials to notify state and federal agencies, taking down several county systems serving nearly 200,000 residents.[^1] Meanwhile, La Vergne, Tennessee's 40,000+ residents cannot pay …
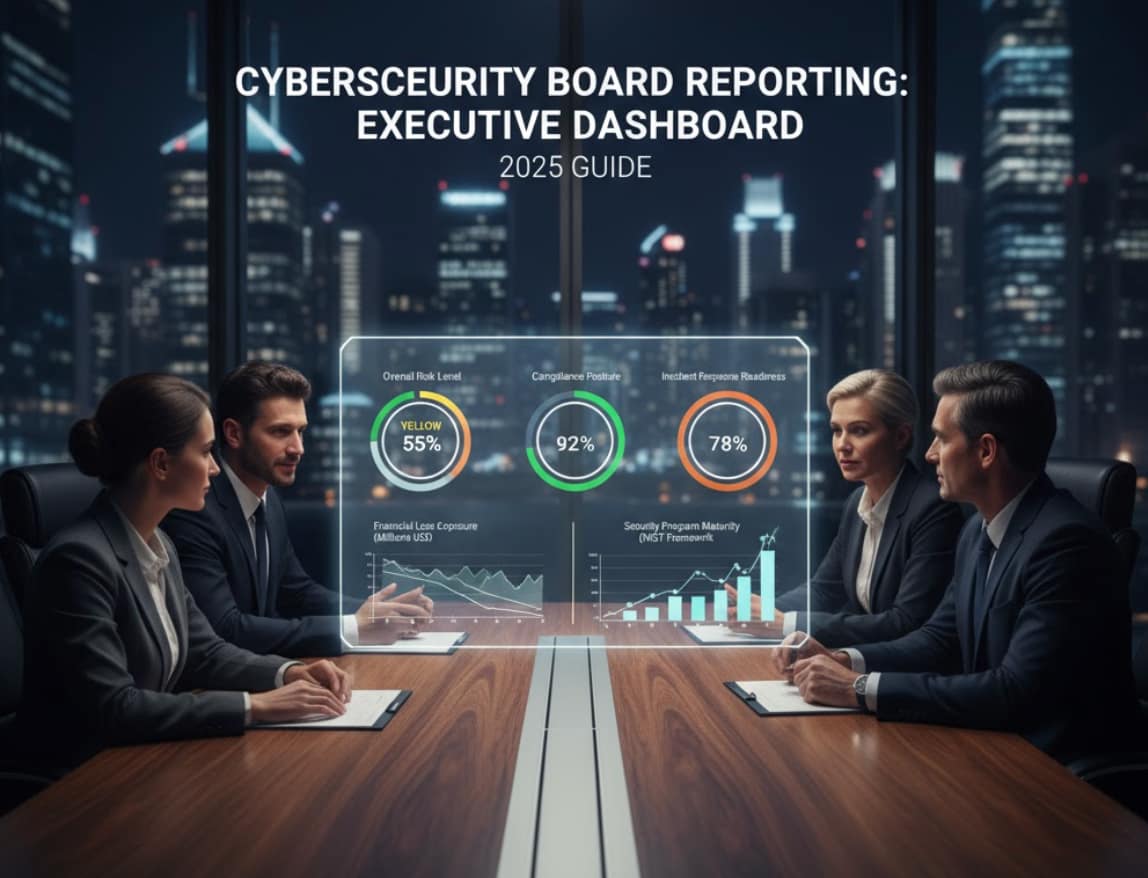
Quick Answer Cybersecurity board reporting transforms complex technical security metrics into business-focused insights that enable directors to make informed governance decisions. With new SEC requirements mandating cybersecurity disclosure and oversight, boards need standardized reporting frameworks that communicate risk in financial terms, demonstrate program effectiveness, and ensure regulatory compliance. Effective cybersecurity board reporting includes risk quantification, …

If you're a B2B technology company, chances are you've encountered the phrase "SOC 2 compliance" during sales conversations, customer security questionnaires, or contract negotiations. For many business leaders, SOC 2 starts as just another compliance acronym—but it quickly becomes a make-or-break requirement for landing enterprise clients. This comprehensive guide explains everything executives need to know …

Introduction: AI Governance – The New Frontier for Cybersecurity Leadership Artificial intelligence has transformed from a futuristic concept to a business-critical technology that's reshaping how organizations operate. However, with this transformation comes unprecedented cybersecurity challenges that demand strategic leadership. CISOs are now in the hot seat and must try to get their hands around both …

Quick Summary MSPs and independent security consultants can add significant compliance revenue without hiring GRC specialists. What You Need: Revenue Potential: Timeline: 3 months from evaluation to first client delivery Who This Serves: Managed service providers, independent security consultants, fractional CISOs, and boutique consulting firms Introduction Managed service providers and independent security consultants consistently hear …
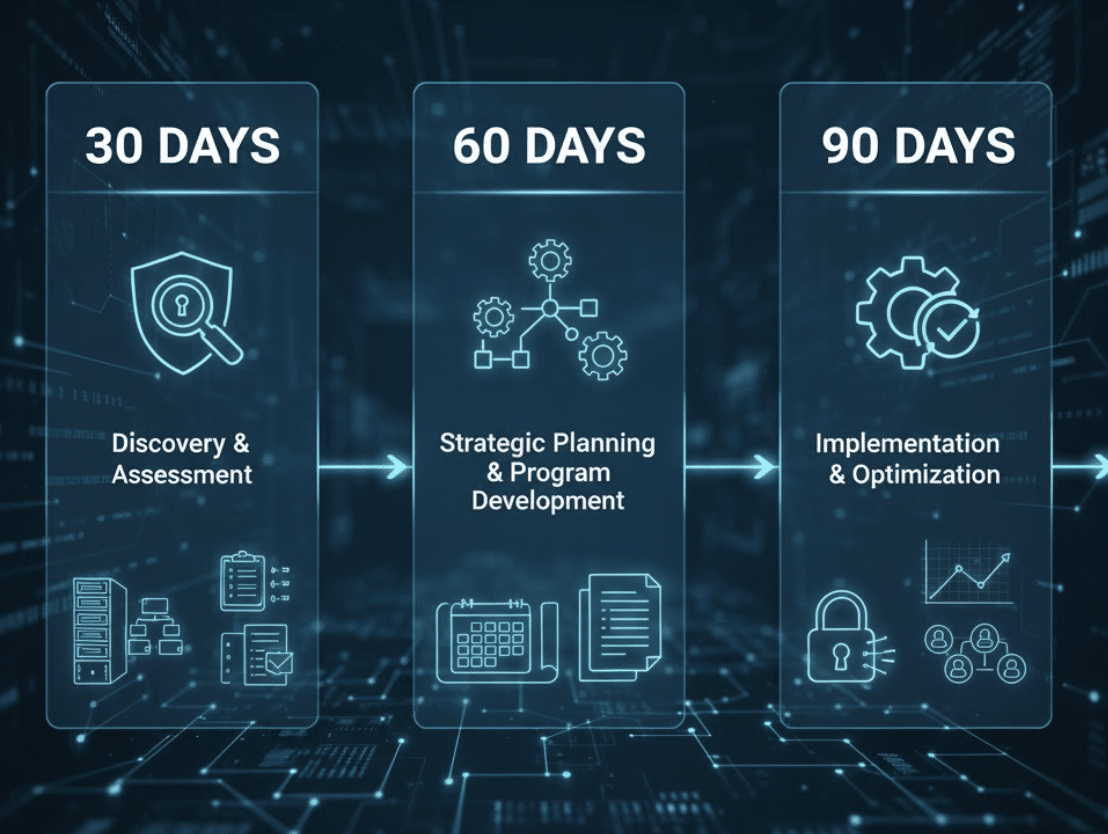
You've made the decision to engage a virtual CISO for your organization. You've completed the selection process, signed the contract, and now you're wondering: what actually happens next? If you're still evaluating virtual CISO providers, consider starting with a free cybersecurity assessment to understand your current security posture and implementation requirements. The first 90 days …

Denver has become a hub for companies embracing remote-first and hybrid work models, from technology startups in RiNo to financial services firms in the Denver Tech Center. While remote work offers advantages in talent acquisition and operational flexibility, it creates cybersecurity challenges that traditional office-based security models cannot address. Companies with distributed teams face expanded …

The Port of Houston handles over 290 million tons of cargo annually, making it America's busiest port by tonnage and a critical gateway for global trade. This massive maritime complex connects Houston to more than 200 countries worldwide, but its strategic importance also makes it an attractive target for sophisticated cyberattackers. Maritime cybersecurity threats have …

Dallas stands as America's energy capital, home to more Fortune 500 energy companies than any other U.S. city. From ExxonMobil's global headquarters to hundreds of independent oil and gas operators, the Dallas-Fort Worth metroplex drives the nation's energy infrastructure. However, this concentration of critical energy assets makes Dallas a prime target for nation-state actors, cybercriminals, …

Quick Answer A virtual CISO (vCISO)—also called fractional CISO, part-time CISO, or outsourced CISO—is an experienced Chief Information Security Officer who provides executive-level cybersecurity leadership on a flexible, part-time basis. Instead of hiring a full-time security executive at $250,000-$400,000 annually, companies engage virtual CISO services for 10-20 hours monthly, accessing the same strategic expertise at …

Quick Answer Dallas financial institutions face unique cybersecurity challenges combining federal banking regulations (GLBA, FFIEC), state requirements, and sophisticated fraud targeting regional banks and credit unions. Effective protection requires specialized cybersecurity programs addressing wire fraud, account takeover attacks, third-party vendor risks, and regulatory examination expectations while maintaining competitive customer service. Financial services in Dallas operate …

Industry Analysis, Cost Comparison & Strategic Insights The Virtual Chief Information Security Officer (vCISO) market represents one of the fastest-growing segments in cybersecurity services, driven by escalating cyber threats, regulatory complexity, and a severe shortage of qualified security executives. This report analyzes publicly available market data, salary trends, and industry dynamics to provide organizations with …

Security vulnerabilities don't announce themselves with warning signs. Most organizations discover critical security gaps only after attackers exploit them—when breaches cost an average of $4.88 million and take 194 days to identify. Yet 68% of organizations conduct security risk assessments irregularly or not at all, leaving themselves exposed to preventable threats. A comprehensive security risk …

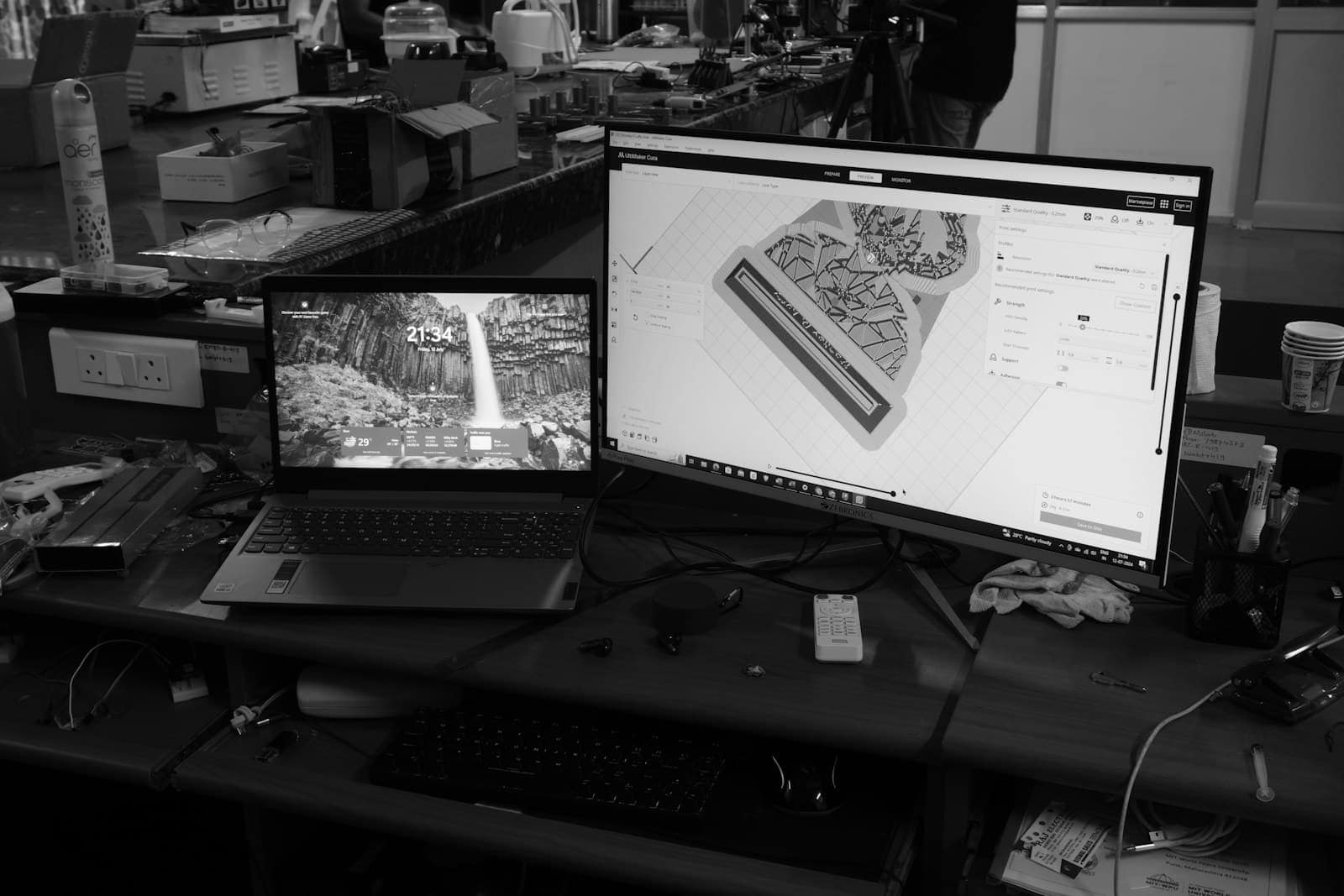
Quick Answer Modern AI-powered GRC platforms can predict risks, validate evidence quality, and automate complex compliance workflows—yet 60% of organizations still manage compliance manually with spreadsheets despite implementing these platforms. The challenge isn't platform capability; it's the strategic oversight gap. AI augments human expertise but cannot replace the business context, auditor relationships, and strategic judgment …

Quick Answer: Penetration testing simulates real-world cyberattacks to identify vulnerabilities in your systems before hackers exploit them. For business leaders, pen testing is essential for compliance (PCI DSS, SOC 2, HIPAA), pre-M&A due diligence, and validating security investments. Costs range from $5,000-$50,000+ depending on scope. Most organizations need annual testing at minimum, with quarterly testing …

Quick Answer: Virtual CISOs provide manufacturing companies with specialized operational technology (OT) and IT security leadership, ICS/SCADA expertise, and regulatory compliance guidance at 50-70% lower cost than full-time CISO hires. Typical engagement includes 20-40 hours per month of strategic oversight, with deep expertise in industrial control systems, supply chain security, and manufacturing-specific compliance frameworks. Manufacturing …

ISO 27001 Certification Guide: Complete Implementation Roadmap for US Companies Your UK enterprise prospect just sent over their vendor security questionnaire. Among the requirements: ISO 27001 certification. You have SOC 2 Type II—isn't that enough? Not for international business. While SOC 2 opens doors to US enterprise customers, ISO 27001 is the global standard that …

Your company just crossed $30M in revenue. Your board is asking about SOC 2 compliance. Investors want 24/7 security monitoring. And your CFO just told you the budget for a full-time CISO and security operations center is… $1.2 million annually. There's a better way. By integrating Virtual Chief Information Security Officer (vCISO) services with a …

The Department of Defense published the final CMMC 2.0 rule on September 10, 2025, effective November 10, 2025. This marks the end of voluntary self-attestation and the beginning of mandatory third-party cybersecurity verification for defense contractors handling sensitive information. The phased implementation runs through 2028, but waiting until your contract explicitly requires CMMC certification is …

Hiring a virtual CISO (vCISO) or fractional CISO is one of the most important cybersecurity decisions your organization will make. The right provider becomes a trusted strategic partner who protects your business, ensures compliance, and enables growth. The wrong choice can waste $60,000-$180,000 annually while leaving critical security gaps that expose your organization to breaches …

The NIST Cybersecurity Framework 2.0 has become the gold standard for organizational cybersecurity, but most small businesses struggle to understand how this enterprise-focused framework applies to their resource-constrained environments. Released in February 2024, the updated framework now explicitly targets organizations of all sizes, making it more accessible than ever for small businesses seeking practical roadmaps …
A Comprehensive Report on Data Breaches, Cybercrime, and Security Threats Facing Texas Businesses Published by BlueRadius Cyber | October 2025 Executive Summary Texas businesses are under unprecedented cyber attack. This analysis of 2024-2025 breach data reveals that Texas ranked #2 nationally in cybercrime complaints, with businesses and individuals reporting $1.35 billion in losses in 2024 …

Austin has become the second-largest startup hub in the United States, with thousands of SaaS companies competing for enterprise customers. But there's a problem: enterprise buyers won't sign contracts without SOC 2 certification. For growing SaaS companies without a Chief Information Security Officer, achieving SOC 2 compliance seems impossible—until you discover virtual CISO services. This …

Quick Answer: Virtual CISOs provide experienced federal security leadership to achieve FedRAMP authorization at 50-70% lower cost than full-time CISO hires. Typical timeline: 12-18 months from gap assessment to Authority to Operate (ATO). Typical engagement: 20-25 hours/month strategic oversight while your team handles technical implementation. Best for: SaaS companies targeting federal agency customers requiring FedRAMP …

Quick Answer: Fort Worth managed security services provide 24/7 SOC monitoring, threat detection, and incident response at significantly lower cost than building internal security teams ($350K+/year for 2-3 analysts). Ideal for DFW manufacturing, healthcare, energy, and financial services companies needing around-the-clock protection without enterprise budgets. Fort Worth businesses operate at the intersection of advanced manufacturing, …

Quick Answer: Virtual CISOs provide experienced security leadership to achieve SOC 2 Type II certification at 50-70% lower cost than full-time CISO hires. Typical timeline: 9-12 months. Typical engagement: 12-20 hours/month strategic oversight while your team handles tactical implementation. Best for: SaaS companies $5M-$50M revenue needing SOC 2 for enterprise sales or investor requirements. Your …

The deal closed 47 days ago. Your PE firm acquired a SaaS company for $75 million. Due diligence showed solid security. Then yesterday: an active breach using an abandoned admin account from the acquired company. Three weeks of undetected access. Customer data exposed. Total damage: $4.2 million in response costs, 120% insurance premium increase, and …

Chicago's manufacturing sector generates over $95 billion annually while employing hundreds of thousands of workers across food processing, machinery, electronics, and industrial equipment production. Yet most mid-market manufacturers face a critical security paradox: sophisticated cyber threats targeting operational technology and intellectual property, but budgets too constrained for a full-time Chief Information Security Officer commanding $250,000-plus …

The decision to transition from virtual CISO (vCISO) services to a full-time Chief Information Security Officer represents a critical inflection point in your company's cybersecurity maturity. This isn't simply a hiring decision—it's a strategic choice that impacts budget allocation, organizational structure, and security effectiveness for years to come. Many executives struggle with this transition timing. …

Manhattan's Financial District houses a significant concentration of alternative investment assets, making it a major global center for private equity and hedge fund operations. These firms face unique cybersecurity challenges that traditional security models can't address—from protecting sensitive due diligence data to securing complex portfolio company networks. Virtual Chief Information Security Officer (vCISO) services provide …

Healthcare practices across the United States face increasing complexity in maintaining HIPAA compliance while delivering quality patient care. The Health Insurance Portability and Accountability Act (HIPAA) requires comprehensive safeguards for protected health information (PHI), with violations carrying penalties ranging from $100 to $50,000 per incident, and potential criminal charges for willful neglect. This comprehensive HIPAA …

Healthcare cybersecurity implementation in Dallas requires specialized approaches that address the unique challenges facing medical practices in one of America's largest metropolitan areas. From UT Southwestern Medical Center affiliates to independent practices throughout the Dallas-Fort Worth metroplex, healthcare providers operate in an environment where cyber threats specifically target patient data while regulatory compliance demands continue …

Austin businesses face increasing cybersecurity threats that can disrupt operations, damage reputation, and result in significant financial losses. A comprehensive IT security assessment helps identify vulnerabilities before attackers exploit them, ensuring your business maintains the strong security posture needed to protect customers, comply with regulations, and support continued growth. This practical checklist guides Austin business …

The energy sector faces an unprecedented cybersecurity crisis. In 2021, the Colonial Pipeline attack shut down the largest fuel pipeline system in the United States for six days, causing widespread fuel shortages and costing the company over $90 million in direct response costs. This wasn't an isolated incident—it was a wake-up call that cybercriminals view …

Web applications power modern business operations, but they're also the primary target for cybercriminals. Over 90% of successful data breaches exploit web application vulnerabilities, costing organizations an average of $4.9 million per incident. The Open Web Application Security Project (OWASP) framework identifies the most dangerous application security risks that every business leader should understand. While …

Every CISO, CEO, and CFO eventually faces the same critical question: should your organization invest in SIEM vs XDR security architecture? After helping Fortune 500 companies and resource-constrained organizations evaluate these decisions through BlueRadius Cyber consulting engagements, including implementations of our Threat Ops platform, the answer isn't about the technology. It's about strategic architecture decisions …
Executive Summary: API security for business leaders isn't just a technical concern—it's a critical business imperative. With APIs handling 83% of web traffic and API-related breaches costing 23% more than average data incidents, understanding and securing your organization's API infrastructure has become essential for protecting revenue, reputation, and regulatory compliance. The digital transformation of modern …

Central Texas cybersecurity demands specialized approaches that address the unique business landscape spanning Waco, Temple, Killeen, and surrounding communities where universities, healthcare systems, manufacturing facilities, and agricultural businesses create diverse threat profiles requiring comprehensive protection strategies. The region's economic foundation—built on major institutions like Baylor University, Scott & White Healthcare, and significant manufacturing operations—presents cybercriminals …

Cybersecurity awareness training has become the cornerstone of modern business protection strategies, transforming employees from security vulnerabilities into your organization's first line of defense. While businesses invest heavily in firewalls, endpoint protection, and advanced threat detection systems, human error remains responsible for over 95% of successful cyber attacks. This comprehensive guide explores how strategic security …
E-commerce cybersecurity represents one of the most critical challenges facing online retailers today, as digital storefronts handle sensitive customer payment data, personal information, and business transactions around the clock. With cyber attacks targeting e-commerce businesses increasing by over 40% annually, retailers from Austin startups to enterprise-level operations across Texas must implement comprehensive security strategies that …

Higher education cybersecurity faces unprecedented challenges as universities and colleges navigate complex digital transformation initiatives while protecting sensitive student data, valuable research assets, and federal funding compliance requirements. From major research universities conducting classified government research to community colleges implementing distance learning programs, educational institutions must balance open academic collaboration with comprehensive security measures that …

SEO Title: Boston Biotech vCISO Services | Fractional CISO Massachusetts Meta Description: Boston biotech vCISO services for FDA compliance, research data protection & IP security. Expert fractional CISO leadership for Cambridge biotech companies. Boston biotech vCISO services have become essential for life sciences companies navigating the complex cybersecurity landscape from Kendall Square to the Seaport …
How strategic digital forensics planning protects enterprise value, reduces liability, and ensures business continuity when cyber incidents occur When cyber incidents strike your organization, the first 72 hours determine whether you face a manageable disruption or a catastrophic business failure. While prevention remains the ideal, the reality of modern cyber threats means that even well-protected …

The cybersecurity consulting landscape has evolved from reactive incident response to strategic business enablement. Modern cybersecurity consulting encompasses everything from executive-level risk assessment to technical security architecture, providing organizations with the expertise needed to navigate an increasingly complex threat environment. This comprehensive guide examines cybersecurity consulting services available to businesses, providing executives with the strategic …

Small businesses in Boston are thriving in one of America's most innovative cities, but with growth comes risk. As more Boston companies embrace digital transformation, they become attractive targets for cybercriminals. Ransomware attacks, phishing scams, and insider threats are no longer distant concerns—they're real dangers that can disrupt operations, compromise sensitive data, and damage customer …

Small businesses in Austin are thriving, but with growth comes risk. As more Austin companies embrace digital tools, they become attractive targets for cybercriminals. Ransomware attacks, phishing scams, and insider threats are no longer distant concerns—they’re real dangers that can disrupt operations, compromise sensitive data, and damage customer trust. Unfortunately, many small businesses lack the …

vCISO cost is one of the most common questions business leaders ask when considering cybersecurity leadership options. With threats growing more sophisticated every day, businesses—especially small and mid-sized enterprises—need expert leadership to safeguard digital assets. But hiring a full-time Chief Information Security Officer (CISO) can be costly and unnecessary for many companies. This is where …

The cybersecurity landscape has fundamentally shifted, making zero trust implementation strategies a critical priority for modern enterprises. By 2025, 60% of companies will consider Zero Trust as a security starting point, and 81% of organizations plan to implement Zero Trust strategies within the next 12 months. Yet despite this widespread adoption intent, developing effective zero …

Cybersecurity audit preparation is critical for every business that relies on IT systems and digital data. Every system carries some risk, and proper preparation ensures your organization is ready when auditors arrive. A well-executed cybersecurity audit gives leaders a clear picture of vulnerabilities, ensures compliance with industry regulations, and provides actionable steps to strengthen defenses. …

Cyberattacks no longer target only the Fortune 500. In Texas, small businesses are now prime prey for ransomware gangs, phishing schemes, and insider threats. A single breach can drain bank accounts, expose customer data, and shatter hard-earned trust. That is why incident response services have shifted from being optional to essential. In 2025, if you …

Cyber threats aren’t slowing down. Every day, businesses face sophisticated attacks, from ransomware and phishing to insider threats and data breaches. The stakes are high: a single breach can compromise sensitive information, damage reputation, and lead to costly downtime. A cybersecurity service provider offers expertise, technology, and processes designed to protect your digital assets, reduce …

SEO Title: Cybersecurity Compliance for SMBs | HIPAA, SOC 2, CMMC Guide 2025 Meta Description: SMB cybersecurity compliance guide for HIPAA, SOC 2, CMMC & FTC Safeguards. Expert strategies to meet regulations while maintaining business growth in 2025. For many small and mid-sized businesses (SMBs), cybersecurity compliance for SMBs has evolved from an optional consideration …
Why Small Businesses Need a Cybersecurity Starter Kit Small businesses are increasingly targeted by cybercriminals. From ransomware attacks to phishing scams, the digital threats facing SMBs are real and growing. Yet, many small businesses lack the resources or expertise to implement comprehensive security measures. A cybersecurity starter kit for small business provides a fast, affordable …
Artificial intelligence is no longer a futuristic concept—it powers enterprise decision-making, automates operations, and drives innovation across industries. Yet with this transformative technology comes a new class of risk: AI cybersecurity threats. As organizations adopt AI at scale, safeguarding these systems is mission-critical. At BlueRadius, we help boards, executives, and security teams navigate this emerging …

Fractional CISO services have become essential for Austin businesses navigating complex cybersecurity challenges without the budget for a full-time executive. As cyber threats intensify and regulatory requirements expand, companies across Austin—from tech startups in the Domain to healthcare practices downtown—need strategic cybersecurity leadership that aligns with their growth trajectory and budget constraints. The traditional approach …

Boston businesses face growing cyber threats. Fractional CISO (vCISO) services provide executive-level cybersecurity leadership without hiring a full-time CISO. Why Boston Businesses Need Fractional CISO Services Boston is a hub of innovation. From biotech in Cambridge to financial institutions downtown, higher education, and tech startups, companies handle massive volumes of sensitive data. Cyberattacks are increasing. …

Dallas businesses operate in a digital environment that’s more interconnected—and more vulnerable—than ever. With cyberattacks growing in sophistication and frequency, companies without dedicated cybersecurity leadership face serious risks. From ransomware attacks to phishing schemes, data breaches can result in financial loss, reputational damage, and regulatory penalties. BlueRadius vCISO services in Dallas provide businesses with strategic …

Cyberattacks don't just hit big corporations. Small businesses in Waco, Texas are now the primary target for cybercriminals — and most never see it coming. If you own or run a small business in Waco, you need cybersecurity protection that fits your budget. The BlueRadius cybersecurity starter kit Waco offers streamlined, effective protection built specifically …
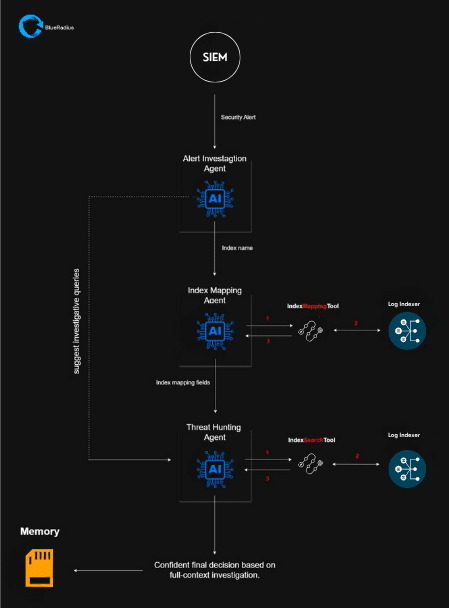
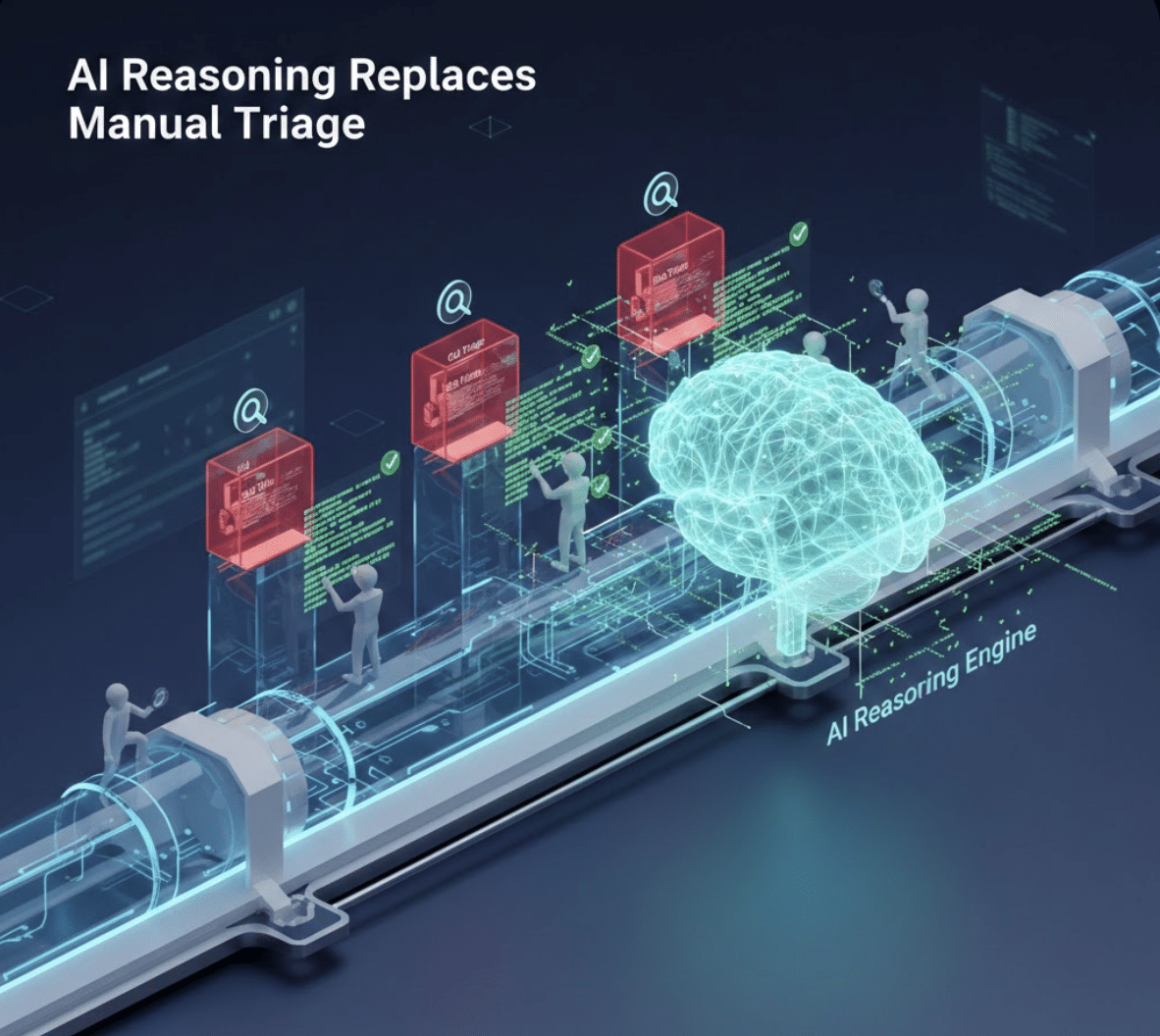
Most security teams are stuck in an endless cycle of alerts, dashboards, and damage control. An alert fires. Analysts dig through fragmented logs, dashboards, and tickets—often for hours—just to figure out what actually happened. That isn’t proactive defense. That’s firefighting. BlueRadius Threat Ops flips that model on its head. Our AI-powered Threat Operations engine doesn’t …

As cybersecurity risks escalate, businesses in Manhattan are facing mounting pressure to protect their digital infrastructure without overextending their budgets. A full-time Chief Information Security Officer (CISO) often comes with a six-figure salary—and a long hiring cycle. For fast-moving companies, that’s not sustainable. That’s where vCISO services in Manhattan come in. What Is a vCISO? …

Seattle is a technology powerhouse—home to enterprise giants, fast-scaling startups, and innovative manufacturers. In such a dynamic environment, your cybersecurity program must keep pace with growth, regulation, and an evolving threat landscape. That’s where a Virtual Chief Information Security Officer (vCISO Services in Seattle) comes in. At Blue Radius Cyber, our vCISO services for Seattle …

— and why that nagging voice telling you to "just muddle through" is very, very wrong. Picture this. You’re running a fast-growing healthcare company, or a punchy mid-sized tech firm. Regulations, it seems, have bred like rabbits: HIPAA here, SOC 2 there, a sprinkle of CCPA to garnish your anxiety. You know cybersecurity compliance is …
A behavioral perspective on why compliance is undervalued, risk is misunderstood, and efficiency is wildly overrated. By Blue Radius Cyber Let’s begin with a modest proposal: in times of recession, economic anxiety, and regulatory uncertainty, the riskiest thing a company can do… is misunderstand risk. Now, I know what you’re thinking. “Of course the cybersecurity …
You know what’s really fun? Governance, risk, and compliance (GRC).Said no one ever. If you're reading this, you probably work in cybersecurity—where risk management and compliance don’t exactly come with a gold star for effort. You’ve lived through the endless audit cycles, the paper trail nightmares, and the risk assessments that take longer than the …

Imagine your business is a castle. The walls are up, but sneaky attackers are finding ways in. They steal secrets, wreck systems, and hold your data for ransom. An MSSP is like hiring a team of expert knights to guard your castle day and night. Cyber threats keep growing. You need better security than basic …
In today's day and age, application security has never been more crucial. As technology advances, so do the tactics employed by cybercriminals, leaving applications vulnerable to a myriad of security flaws. Understanding these vulnerabilities is the first step in shielding your applications from malicious attacks. “The single biggest existential threat that’s out there, I think, …

Imagine navigating a bustling city without a map—now, that's akin to running a modern business without the blueprint of cyber insurance. In today's digital age, where data breaches and cyber threats are as frequent as daily traffic, businesses can't afford to ignore the protective power of cyber insurance. Take a moment to consider the staggering …

Imagine a world where staying connected from the most remote places is as simple as powering on your smartphone. Satellite and direct-to-device communications are transforming telecom & security, revolutionizing connectivity. But how does this cutting-edge technology impact traditional telecommunications? “The future of communication is no longer grounded—it's in the skies.” Today, we'll explore how satellites …

In the bustling business hub of Seattle, companies are constantly navigating a complex web of regulatory compliance requirements. Whether you’re a startup developing cutting-edge technology or a well-established firm in the finance sector, staying compliant is crucial to avoid hefty fines and reputational damage. Yet, achieving this can be overwhelming and resource-intensive. “Compliance doesn’t have …
In today's evolving digital landscape, the cybersecurity threats small businesses will face is larger than ever. As an executive or part of an IT team, understanding these emerging threats isn't just beneficial—it's crucial. By being proactive rather than reactive, you can significantly enhance your organization's resilience against potential breaches. “The greatest threat to our planet is …

In today's digitally driven world, cybersecurity is not just a priority but a necessity for businesses of all sizes. With cyber threats becoming more sophisticated, the stakes are higher than ever. This is where cybersecurity consultants come in. Maximizing the ROI of Cybersecurity Consulting Services is crucial, as engaging with these experts can transform your …

Managed security services Seattle tech ecosystem integration has become critical for protecting the region's most innovative companies. Seattle's technology ecosystem represents one of the most dynamic and innovative business environments in North America, where managed security services Seattle tech ecosystem leaders rely on for comprehensive protection. From global giants like Microsoft and Amazon to thousands …

The security of our water utilities is of paramount importance. As organizations operating within the water utility sector, you bear the critical responsibility of safeguarding not just infrastructure, but the very essence of life—water. Navigating the myriad of security regulations and standards can seem daunting, but it's essential for both compliance and the assurance of …

Your startup is built to scale rapidly, but is your cybersecurity keeping pace? While you're focused on product development, customer acquisition, and fundraising, cybercriminals see growing companies as attractive targets with valuable data but often inadequate security measures. The challenge isn't just protecting what you have today—it's building security that scales seamlessly as your team …

Executive Summary: Data in transit security protects your most valuable information while it moves between systems, networks, and locations. With over 70% of data breaches involving data in motion, understanding and implementing robust data in transit security measures has become essential for protecting business operations, ensuring compliance, and maintaining customer trust across all industries. Every …

Data breaches are not a question of if but when. Any size of organization is a target and even the most secure of systems can have vulnerabilities. An incident response plan is key to minimising damage, getting back to business as usual and maintaining stakeholder trust after a breach. This article covers the key components …

As the digital world rapidly evolves, organizations are compelled to tackle a multitude of cybersecurity challenges while expertly managing their budgets. Pairing a virtual Chief Information Security Officer (vCISO) with a Managed Security Service Provider (MSSP) creates a strategic synergy, achieving both enhanced security and financial efficiency. This approach not only strengthens security postures but …

vCISO vs traditional CISO represents a critical strategic decision for Seattle businesses establishing cybersecurity leadership. This choice between virtual CISO services and full-time Chief Information Security Officer hiring significantly impacts budget allocation, security effectiveness, and business agility in Seattle's competitive technology environment. Understanding the differences between traditional CISO and vCISO models helps Seattle companies make …

In the complex world of mergers and acquisitions (M&A), the stakes are incredibly high. Financial gains, corporate restructuring, and strategic positioning drive these business decisions. However, with such high stakes comes equally high risks, and one significant, evolving threat is the challenge of cybersecurity in mergers and acquisitions, including cyber-attacks strategically targeting M&A activities. Cybercriminals …

In the dynamic world of technology, businesses in Austin, Texas, face unprecedented challenges in safeguarding their digital assets. As cybersecurity threats continue to grow in both sophistication and frequency, managing these risks requires more than a robust IT team. Enter Managed Security Services Providers (MSSPs)—a comprehensive solution offering expertise, vigilance, and peace of mind to …

Managed security services in Seattle provide comprehensive cybersecurity protection for businesses navigating the Pacific Northwest's complex threat landscape. As Seattle's technology sector continues expanding with companies like Microsoft, Amazon, and thousands of startups, the need for professional security management has become critical for business survival and competitive advantage. Seattle businesses face unique cybersecurity challenges including …

Imagine waking up to discover that your favorite online retailer can no longer deliver your order because of a cyberattack that compromised cybersecurity in supply chain operations overnight. In today's interconnected world, the integrity and efficiency of supply chains hinge heavily on robust cybersecurity measures. With the ever-increasing sophistication of cyber threats, securing these complex …

As the world embraces the transformative potential of 5G technology, businesses are unlocking unprecedented opportunities for speed, connectivity, and innovation. However, this technological leap also ushers in a complex landscape of cybersecurity threats that could jeopardize telecommunications infrastructure. In this new era, understanding the importance of security in 5G networks and mitigating these risks is …

Organizations face increasing pressure to protect themselves from advanced cyber threats. Cost-effective cybersecurity leadership, provided by a Virtual Chief Information Security Officer (vCISO), offers an effective solution through expert external guidance. This approach allows companies to tailor their security strategies to today's complex challenges. “Virtual CISOs are cost-effective solutions for organizations to gain executive security …

Assessing your company's cybersecurity needs is crucial for executives today, as cyber threats are constantly evolving. This section aims to explain essential cybersecurity concepts in simple terms, preparing leaders to effectively protect their organizations' critical assets. By gaining this knowledge, leaders can not only secure their companies but also promote a culture of security awareness …
"In the world of cybersecurity, the key to winning is not just technology – it's knowledge." This quote, often attributed to experts in the field like Bruce Schneier, highlights the essence of effective information security. As cybersecurity threats evolve, it becomes clear why robust information security is crucial in a digitally connected environment. By strategically …

Imagine you’re building a fortress to protect your kingdom (your business) from an ever-growing army of invaders (cybercriminals). Some guards patrol the walls, ensuring no one sneaks in, while others actively monitor threats and upgrade defenses in real-time. This is the fundamental difference between cybersecurity services vs managed security services. Let’s break it down to …

"It takes 20 years to build a reputation and a few minutes of a cyber incident to ruin it." – Stéphane Nappo Small and medium-sized businesses (SMBs) in Dallas often assume their size shields them from cybercriminals, but this belief couldn’t be further from the truth. As cybersecurity expert Bruce Schneier wisely stated, "Security is …

Why Cybersecurity Consulting Matters The types of cyber threats businesses face are constantly evolving. From sophisticated hacking groups targeting major corporations to smaller, more agile attackers exploiting vulnerabilities in everyday business software, no organization is safe. Ransomware continues to be one of the most prevalent threats, with cybercriminals demanding payments in exchange for decryption keys …

"The question isn't if you'll be attacked, but when. Make sure you're ready."– Kevin Mitnick, renowned cybersecurity expert As a business in Seattle, you're no stranger to the constantly evolving landscape of cybersecurity threats. Whether you're a small startup, a medium-sized business, or a larger enterprise, your company’s data and networks are always at risk. …

"Security is not a product, but a process." – Bruce Schneier The oil and gas industry is a critical part of the global economy, and as such, it is an attractive target for cybercriminals. With the increasing complexity of digital technologies used across the sector, managing information security challenges in oil and gas is more …

Small business cybersecurity in Austin has become a critical survival factor as cyber threats increasingly target companies across the city's thriving business ecosystem. From tech startups in the Domain to family-owned restaurants on South Congress, Austin small businesses face sophisticated cyberattacks that can devastate operations, destroy reputations, and force permanent closure. The dangerous misconception that …

"It takes 20 years to build a reputation and a few minutes of cyber-incident to ruin it." – Stéphane Nappo Small and medium-sized businesses (SMBs) often believe they’re too insignificant to attract the attention of cybercriminals, to need a cyber security firm. Unfortunately, this couldn’t be further from the truth. As cybersecurity expert Bruce Schneier …

With the increasing integration of digital technology into financial systems, family offices, which manage the wealth and investments of high-net-worth families, face a growing number of cyber threats. The protection of generational wealth is more complex than ever, as cybercriminals become more sophisticated in their attacks. This blog will guide you through a roadmap to …

Achieving HIPAA compliance is essential for protecting patient data and maintaining trust in healthcare organizations. This guide explores robust cybersecurity solutions, best practices, and tools to help safeguard Protected Health Information (PHI) while meeting HIPAA regulatory standards. Learn how to implement effective strategies to secure your systems and stay compliant in today's digital landscape.

In healthcare, keeping patient information safe is very important. Healthcare clinics have lots of sensitive information, like medical records and insurance details. This information is valuable, which makes clinics a target for people who want to steal it. If this data is stolen, it can cause a lot of harm. This blog will explain why …

In today’s increasingly digital world, cybersecurity has become a paramount concern for wealth management firms. As financial services migrate online and the digital landscape continues to expand, wealth managers are facing a growing array of cyber threats. With vast amounts of highly sensitive financial data and significant assets at stake, implementing robust cybersecurity measures is …

Austin, Texas—fondly known as the Live Music Capital of the World—is a vibrant city where tech innovation harmonizes with the cultural buzz of live music. This thriving metropolis attracts companies of all sizes, from startups to established enterprises, all eager to be part of its dynamic ecosystem. However, with this growth comes a pressing concern: …

Cybersecurity risk management is more important than ever. Discover how a Virtual Chief Information Security Officer (vCISO) can provide the expertise you need without the full-time commitment.
Discover how regular penetration testing can safeguard your business from costly cyber attacks. Want to save money and enhance security? Learn more here.

How can we secure our vital water and utility networks? Discover strategies to protect critical infrastructure and ensure safety and reliability for all.

Discover essential IoT security tips for small and mid-sized businesses. Are you prepared to tackle potential risks and protect your connected devices effectively?

In an era where data breaches are becoming increasingly common, businesses must adopt proactive measures to safeguard sensitive information. This is where threat intelligence comes into play. By leveraging timely and relevant data about potential threats, companies can stay one step ahead of cybercriminals. But how exactly can businesses integrate threat intelligence into their security …

In an era where digital connectivity is more crucial than ever, telecom companies find themselves at the forefront of innovation and expansion. The surge toward cloud computing offers a new realm of possibilities—providing scalability, flexibility, and enhanced performance. However, this shift also introduces unique cybersecurity challenges that are as complex as they are critical. As …

Discover strategies to secure critical infrastructure. How can we protect water and utility networks from threats? Learn actionable steps to enhance their safety.

Discover how to safeguard your business in Austin with a robust data protection strategy. Are you ready to secure your sensitive information effectively?

In today's fast-paced digital world, schools are increasingly relying on technology to enhance both teaching and learning experiences. Yet, managing complex IT infrastructures poses significant challenges for educational institutions. From ensuring network reliability to safeguarding sensitive student records, schools face a myriad of obstacles in maintaining an effective IT environment. Herein lies the importance of …

Imagine a dynamic legal firm, bustling with activity, where every day brings new challenges and opportunities. As a legal professional, your focus is on delivering impeccable service to your clients, but the administrative and IT burdens can often get in the way. Integrating managed IT services into your operations can be a game changer, simplifying …

Essential strategies for healthcare providers to safeguard patient data and maintain operational continuity in 2025 On February 21, 2024, Change Healthcare—one of the nation's largest healthcare payment processors—fell victim to a devastating ransomware attack that sent shockwaves through the entire healthcare industry. Within hours, prescription processing ground to a halt, insurance claims couldn't be verified, …

Have you ever wondered what lies beneath the surface of your daily internet searches? Beyond the websites that dominate our online interactions lies a hidden world — The Anatomy of the Dark Web. As a business executive, understanding its structure and functions is crucial to safeguarding your organization from potential risks. “It's not just a …

How the 5 most dangerous cyber threats shut down business operations and what you can do about it Cyber threats aren't just theoretical risks anymore—they're operational emergencies that can shut down businesses within hours and cause lasting damage to revenue, reputation, and customer trust. From manufacturing plants to healthcare facilities, no industry is immune to …
Imagine a world where cyber threats are not just lurking threats but are aggressively evolving, targeting the very core of your network infrastructure. As digital landscapes expand, so does the sophistication of cyberattacks. This evolution in threats calls for equally advanced defenses, and here's where Artificial Intelligence (AI) steps in as a beacon of hope …

Navigate the complexities of cyber incidents. Are you aware of the legal and regulatory steps required to ensure compliance and protect your organization?

Discover how businesses can adapt digital strategies to support remote workforces. Are you ready to transform your operations for the remote work era?
Discover how data breaches can tarnish your brand's reputation and explore actionable strategies to mitigate the damage. Can your company afford the risk?

Motivating IT teams to push boundaries and achieve peak performance isn't just a matter of providing the latest tools and technologies. It's about creating an environment where creativity, collaboration, and continuous improvement thrive. How can you, as a leader, nurture such an environment? Here are some key strategies that can help guide your IT teams …
Discover how AI revolutionizes cybersecurity by swiftly detecting and responding to threats. Can artificial intelligence be the key to a safer digital world?

In today's digital age, the dark web poses significant threats to businesses of all sizes. Business owners in Texas are no exception. Criminals on the dark web exploit vulnerabilities in your systems to steal sensitive information, disrupt operations, and even hold your data hostage through ransomware attacks. While these threats may seem distant or unlikely, …

Strategic cybersecurity that enables growth rather than restricts it High-growth companies face a critical challenge: How do you get enterprise-grade cybersecurity protection while maintaining the speed and agility that drives your success? Unlike generic security advice, scaling organizations need strategic approaches that evolve with growth. Whether you're preparing for Series B funding, scaling nationally, or …

In today's digital world, cyber threats are always evolving. To protect sensitive data, maintain compliance with industry standards, and prevent potential cyber attacks, assessing an organization's IT security controls is crucial. But where do you start? This comprehensive guide to IT Security Controls Assessment provides a step-by-step process, valuable resources, and best practices to ensure your organization's security posture remains robust. By taking a proactive approach to cybersecurity and implementing recommended practices, organizations can safeguard their assets, reduce the likelihood of successful cyber attacks, and maintain the trust of their stakeholders.
Uncover the secrets to boosting network security and IT support through cloud technology for businesses in Fort Worth, Texas. This guide offers best practices, strategies, and tips for protecting your data and improving IT services.

Discover 5 key cybersecurity basics for businesses in Temple, Texas. Learn about Identity, PAM, Authentication, Authorization, and Credential Management to enhance your business security.

Discover expert Managed IT Services, comprehensive IT Support, and robust Cybersecurity Defense in Austin, TX. Safeguard your business with Blue Radius Cyber.

Cybersecurity vulnerability management has become a cornerstone of business protection for Austin companies navigating an increasingly complex threat landscape. Recent high-profile incidents, including the widespread CrowdStrike update disruption, have demonstrated how even routine security updates can create significant business disruptions when proper vulnerability management protocols aren't followed. For Austin's thriving business community—from tech startups in …
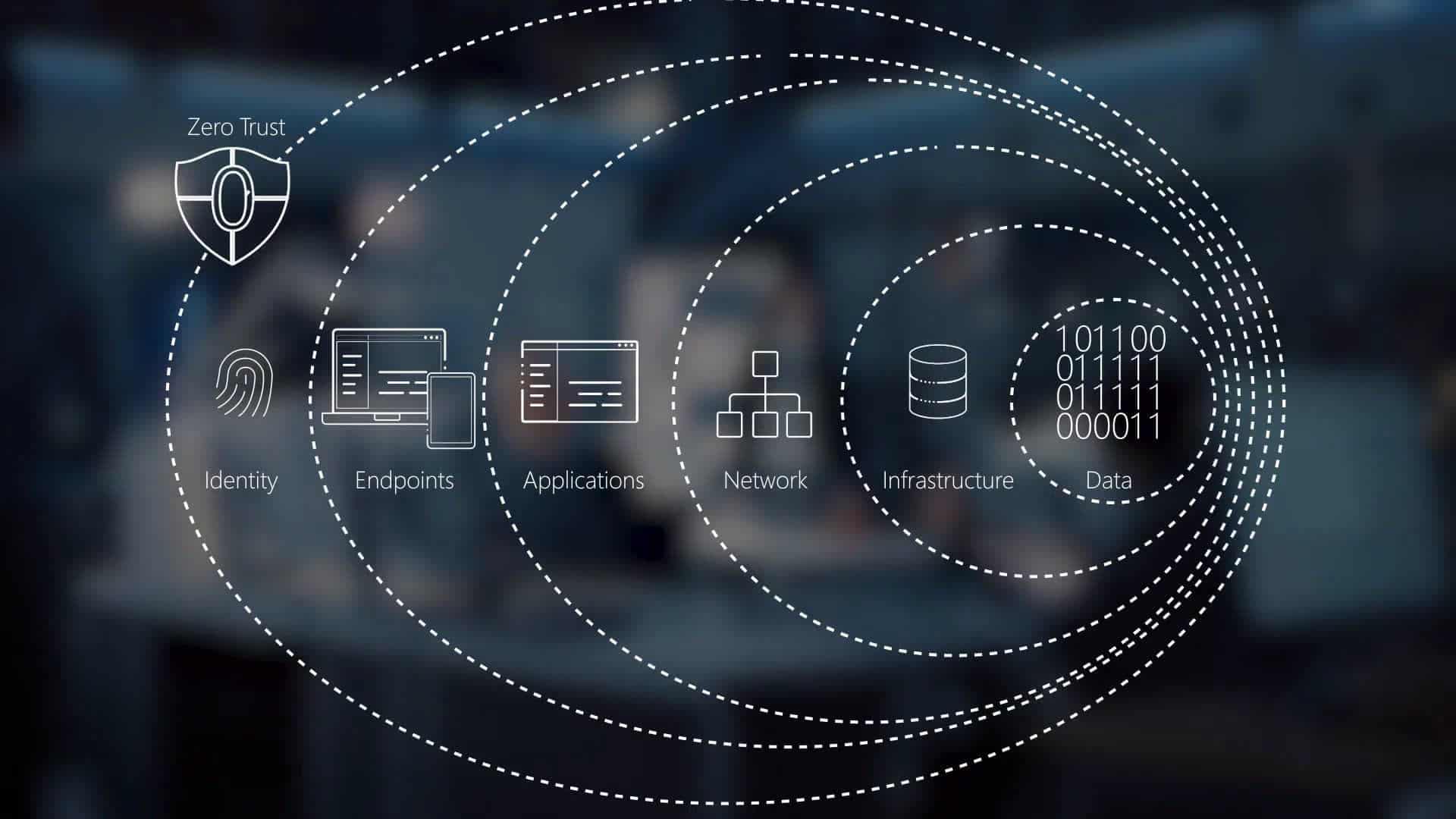
In today's digital landscape, traditional security measures are no longer sufficient to protect against evolving cyber threats. Enter Zero Trust Architecture, a security model that revolutionizes computer networking by enforcing the principle of "never trust, always verify." This comprehensive guide explores the core components of Zero Trust, its implementation best practices, and real-world case studies, illustrating how this approach can significantly enhance security, reduce risks, and ensure data integrity in various digital environments. Learn how adopting Zero Trust Architecture can transform your organization's security posture and safeguard your critical assets.

Ransomware is a growing threat to businesses worldwide, and Waco, Texas, is no exception. This comprehensive guide delves into the fundamentals of ransomware, its impact, and how a local Managed Security Services Provider (MSSP) like Blue Radius Cyber can protect your business. Learn about the various types of ransomware, the financial and operational consequences of an attack, and the critical role MSSPs play in providing advanced threat detection, employee training, and customized security solutions. Discover the benefits of partnering with an MSSP to ensure your business remains secure and resilient against cyber threats.

How C-level executives can build comprehensive cloud security frameworks that protect business value while enabling digital transformation In March 2024, a misconfigured cloud storage bucket at a major healthcare provider exposed 11 million patient records for six months before discovery. The breach cost the organization $47 million in regulatory fines, legal settlements, and remediation efforts. …

In today's digital age, small and medium-sized businesses (SMBs) are increasingly turning to the cloud to streamline operations, enhance flexibility, and boost productivity. If you're new to the concept or considering its adoption for your SMB in Texas, this guide will help you grasp the fundamentals and discover its potential benefits. What is Cloud Computing? …

Discover how Austin businesses excel with IT managed services. Ready to boost efficiency and security? Learn why your company needs a trusted IT partner today.

Phishing attacks are a growing threat to businesses of all sizes. Discover how Blue Radius Cyber can help protect your company with top-notch security solutions and expert guidance.

Discover the top managed IT services in Fort Worth, TX by Blue Radius Cyber. From network security to IT support, we offer comprehensive solutions for your business needs. Managed IT Services in Fort Worth, TX: Your Ultimate Guide by Blue Radius Cyber In today’s fast-paced digital world, having reliable IT support is crucial for any …

Explore the exceptional managed IT services offered by Blue Radius Cyber in Waco, TX. Our team provides comprehensive IT support, ensuring your business stays secure and efficient.